Hardening Industrial IoT Devices to Prevent Cyber Attacks
 In 2016, a Distributed Denial of Service (DDoS) attack against Dyn was launched from more than 100,000 compromised devices, exposing the vulnerability of Internet‑of‑Things (IoT) endpoints. The attack disrupted critical online services worldwide, sparking a new focus on network security and the need to secure the growing ecosystem of connected devices.[DYN]
In 2016, a Distributed Denial of Service (DDoS) attack against Dyn was launched from more than 100,000 compromised devices, exposing the vulnerability of Internet‑of‑Things (IoT) endpoints. The attack disrupted critical online services worldwide, sparking a new focus on network security and the need to secure the growing ecosystem of connected devices.[DYN]
In this blog, we examine a multi‑layer product‑security architecture that protects industrial IoT network devices—routers, switches, and wireless access points—against sophisticated threats. We outline hardening requirements that reduce the risk of data breaches and software intrusions, even when attackers are determined to bypass conventional defenses.
Malicious attacks are not confined to consumer IoT. In recent months, a manufacturing plant in North Carolina experienced a costly production outage when hackers deployed corrupted firmware designed to sabotage operations and demand ransom. This incident illustrates the financial and operational impact of data‑breach attacks, a trend highlighted in the 2017 Cost of Data Breach Study by Ponemon.[Ponemon]

Industrial IoT designers must embed device and platform integrity—access‑control policies, threat‑detection, and mitigation mechanisms—directly into routers, switches, and outdoor wireless points. Failure to address these elements can grant attackers a foothold that leads to data breaches or broader infrastructure compromise, as seen in incidents in Ireland.[Ireland]
According to Cisco Trustworthy Systems At‑a‑Glance, the threat landscape has evolved, making device hardening an indispensable first step toward trustworthy systems. It safeguards against:
- Hardware tampering and rogue devices: Prevents unauthorized hardware from joining the network and eliminates the risk of counterfeit components that could introduce anomalous behavior.
- Software tampering: Blocks malicious code that could exfiltrate data or alter device functionality.
- Unauthorized user access: Restricts privileged accounts from gaining unauthorized control over devices and the network.
- Unauthorized network access: Stops attacks such as sniffing, reconnaissance, and man‑in‑the‑middle (MITM) that compromise data confidentiality and integrity.
- DDoS via protocol manipulation: Mitigates floods that overwhelm legitimate traffic, including ARP, DHCP, routing, and Layer 3–4 spoofing or header manipulation.
- Malware in application layers: Guards against viruses, ransomware, and protocol exploits that can corrupt data or disrupt operations, especially in Fog and Edge environments.
How Industrial IoT Security Is Built
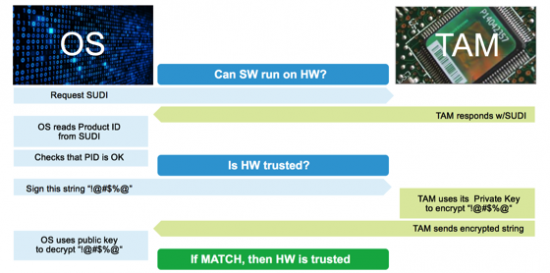
The Cisco Industrial IoT portfolio is engineered from the ground up using the Cisco Secure Development Lifecycle. Each hardware platform incorporates an ACT2 chipset that provides a Secure Unique Device Identity compliant with IEEE 802.1AR, along with an X.509 certificate chain provisioned at manufacturing. This embedded certificate anchors trust in the boot chain, enabling continuous verification of boot‑code integrity, as illustrated in Figure 1.[CSDL]
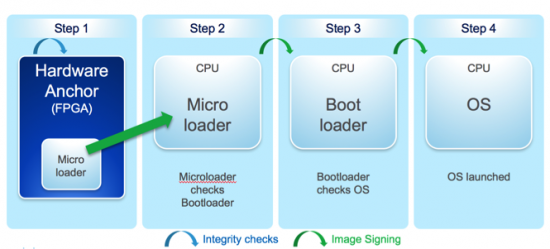
Software integrity is enforced through image signing and Secure Boot. Key features include:
- Golden bootloader images are permanently stored on read‑only flash, sealed in epoxy and tamper‑evident, and signed.
- FPGA bootloaders are signed and validated by Cisco Secure Boot using certificates embedded in ACT2.
This architecture protects the boot sequence from alteration, booting from unauthorized devices, bypassing integrity checks, or injecting persistent malicious code. Every stage of the boot process, shown in Figure 2, is cryptographically chained to guarantee integrity all the way through the system.
After boot, device integrity can be validated using Cisco IOS Software Integrity Assurance, with platform‑specific commands detailed in the documentation.[CSIA]
Subsequently, hardening the software configuration—guided by Cisco IOS hardening best practices—protects user access and the network control plane from exploitation.
While perfection is unattainable, a proactive approach that protects against known threats and mitigates unknown risks is the most effective strategy.
We welcome your insights. Share the challenges your organization faces in the comments below.
Internet of Things Technology
- 7 Essential Steps to Secure Your Home IoT Network
- Smart Security: Expert Strategies to Shield Your Home IoT Devices from Hackers
- How Intelligent Networks Drive Business Efficiency and Growth
- Deploying and Managing Wireless Sensor Networks in the Enterprise
- The Rising Threat of Kill‑Chain Attacks on IoT Devices – What Businesses Must Know
- Detecting Cyber Attacks: A Practical Guide for Your Company
- Protect Your Business: Expert Cybersecurity Strategies for Manufacturers
- Assessing the Security of Your Shop Floor Network: Are You Prepared?
- Proven Techniques for Corrosion Prevention in Metal Equipment
- Prevent Air Compressor Overheating: Proven Strategies for Reliable Performance



