







Industrial Internet of Things
In this article, we’ll study the basic structure of a Verilog module, look at some examples of using the Verilog “wire” data type and its vector form, and briefly touch on some differences between VHDL and Verilog. In this article, we’ll study the basic structure of a Verilog module, look
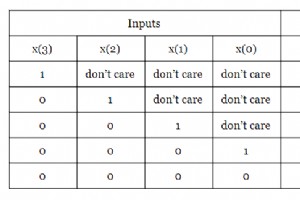
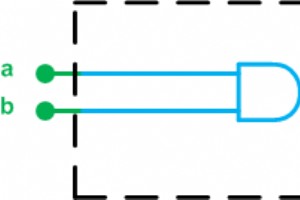
This article explains how to model combinational logic in Verilog, covering the conditional operator for truth‑table implementation and the powerful “always” block for concise design. In this guide, we walk through the key techniques for describing combinational circuits in Verilog. First, we revis
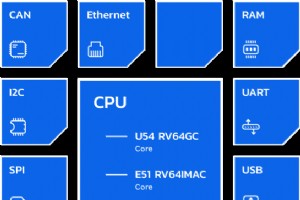
This article demonstrates how open‑source functional simulators such as Antmicro’s Renode become indispensable in hardware‑software co‑design. Embedded systems are evolving rapidly, and next‑generation SoCs are growing in complexity. According to Semico Research, this complexity drives longer design
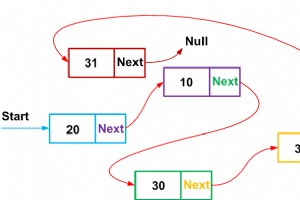
Structures are a cornerstone of efficient embedded C programming. In this article, we’ll explore their practical applications, the syntax for declaring them, and the impact of data alignment on memory usage. By strategically ordering structure members, you can often reduce the footprint of your data

Sensors Expo is returning to the McEnery Convention Center, San Jose, CA from June 27 – 29, with its new name — Sensors Converge. There are nine conference tracks that highlight the different applications for sensors, but if you take a closer look, they share a common theme. It’s all about intellige
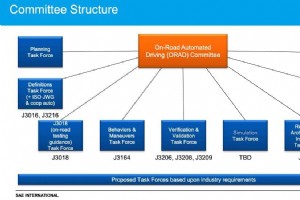
Before an autonomous vehicle can take the road, it needs to be tested for as many scenarios as possible. Simulation software and model-based development tools can create virtual test-drive environments. HIL, or hardware-in-the-loop, testing connects a controllers real signals to a test system that
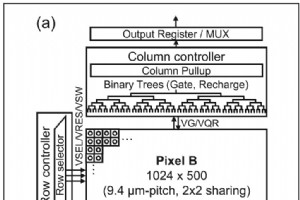
Picture a camera designed to capture images with a resolution of a single photon at 24,000 frames per second. Thanks to an electronic shutter that can stay open for only 3.8ns and that can be synchronized with fast laser pulses with a duration of only a few picoseconds, one can literally see light p
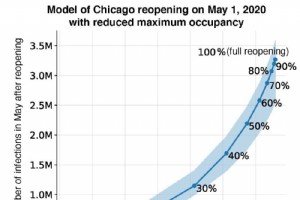
As COVID-19 cases increase across the country, city officials have been given the difficult balancing act of preventing the spread of infections and supporting businesses. A computer model from Stanford University demonstrates mobility and contact patterns in a way that its creators hope will help t

Explore the world of cloud migration: Learn about its benefits, drivers, types, challenges, and best practices. Discover how the Cloud Institutes Cloud Computing Bootcamp empowers aspiring cloud professionals. In todays fast-evolving digital landscape, cloud computing has become the g

Discover seven effective ways to stay up to date during a cloud migration process. Learn from industry experts, attend conferences, and explore training programs to ensure a successful transition. In todays rapidly evolving technological landscape, cloud migration has become a crucia

Discover six effective strategies to gain managements buy-in for your cloud migration plan. Learn how to address concerns, showcase benefits, and navigate the path to cloud adoption successfully. In todays fast-paced business landscape, moving to the cloud has become a crucial step fo

Discover seven essential ways to keep your cloud data secure in 2024. Learn about multi-factor authentication, encryption, access controls, and more. As we step into the year 2024, the importance of data security has never been more critical. With the rapid advancement of technology

Karen Panettas engineering journey led her to identify critical bias in facial recognition systems and champion transparent technology that protects human welfare. By Esther Shittu, News Writer Shaun Sutner, Senior News Director

The vendor has moved quickly to incorporate technologies such as vector search that are integral to generative AI. By Shaun Sutner, Senior News Director Esther Shittu, News Writer Published: 15 Jul 2025 MongoDB awak

The AI vendors director of product marketing says the company first focused on large chips and later turned attention to ramping up inferencing. By Esther Shittu, News Writer Shaun Sutner, Senior News Director Published:
Presented byModerator: Brandon DunlapAbout this talkJoin us for a deep dive into Systems Security Certified Practitioner (SSCP), the security operations and network security credential from ISC2, creator of the CISSP. As organizations continue to pursue digital transformation initiatives, the threa