Securing Industrial IoT with Intel SGX: An Overview of DDS Security

Part 1 of a Multi‑Part Series
Protecting mission‑critical industrial IoT environments demands security that scales from the edge to the cloud, spanning multiple systems and suppliers. As a lead author of the OMG DDS Security standard, RTI has helped define the essential requirements for safeguarding distributed environments. DDS Security plugins deliver robust, data‑centric protection for data in transit, while RTI Connext DDS Secure provides a proven, trusted connectivity framework that secures systems with flexible, fine‑grained controls and optimal performance from device to cloud.
Security remains a complex challenge. Although RTI’s Connext DDS framework incorporates high‑grade software security, our research team is actively exploring additional layers to fortify IIoT deployments. In this series, we share insights from RTI Research on innovative security approaches.
Security expert Jason Upchurch examines hardware mechanisms that safeguard applications on untrusted systems. He focuses on Intel SGX® within the context of RTI Connext® DDS Micro and Security Plugins, pushing the boundaries of protection.
Let’s dive in.
What is SGX and Why Does it Matter?
SGX (Software Guard Extensions) is an Intel ISA extension that offers a Trusted Execution Environment (TEE) for running applications handling sensitive data. While Intel processors are not dominant in IIoT devices, they frequently appear in server rooms that underpin many IIoT architectures. These server‑side applications are high‑value targets for attackers, making SGX a valuable tool for securing critical data flows.
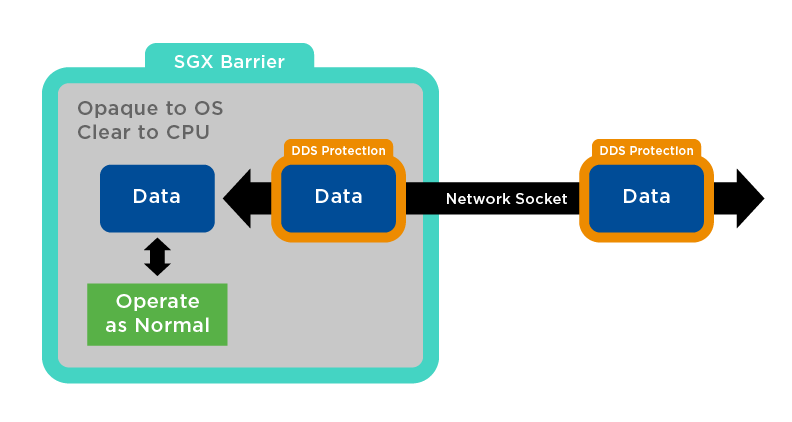
Figure 1: Connext DDS Secure Inside SGX Space
Over‑the‑Wire Security May Not Be Enough
Consider the classic Alice‑and‑Bob scenario: messages travel over a network that an eavesdropper, Eve, could intercept. While encryption protects data in transit, real‑world attackers often compromise the endpoints themselves. As a former investigator of large‑scale intrusions, I have seen that Eve rarely captures encrypted traffic but frequently steals secrets from compromised systems.
In practice, Alice and Bob rely on a multitude of components—operating systems, applications, firmware, and networking hardware—to convey messages. The Trusted Computing Base (TCB) for such a system can encompass hundreds of elements from different vendors, making it difficult to trust the entire stack.
As one security professional once remarked, “It’s like building a steel door with elaborate locks on a house with paper walls.”
To mitigate this risk, the industry adopts a strategy of isolating the minimal set of components that must be trusted, certifying each, and ensuring no unauthorized code enters the TCB.
Security at the Endpoint (and Every Point in Between)
Today’s computing environments balance rich functionality with security. In IIoT, developers often favor widely supported, feature‑rich operating systems for cost and compatibility reasons, which enlarges the TCB. To reconcile these demands, many devices now run a standard OS alongside a separate Trusted Execution Environment (TEE).
Typical TEEs operate with two parallel operating systems: a rich OS for general tasks and a secure OS for sensitive operations. The transition between them is hardware‑controlled and verified through mechanisms such as root‑of‑trust chain loading.
SGX offers a distinct approach. Its TCB is limited to the CPU and the application itself, eliminating the need to trust an OS, firmware, hypervisor, or BIOS. The only software that must be trusted is the application, and the trust chain is only three links long—Root Attestation, CPU, Application—providing a substantially smaller attack surface.

Figure 3: Attack Surface in an SGX Environment
In my experiments, I run a DDS application inside an SGX enclave on a vanilla Ubuntu 16.04 system. Data encrypted by DDS Secure arrives at the OS, is then forwarded into SGX, where the encryption is removed and processed by the application in an isolated, opaque environment. The results are re‑encrypted with Connext DDS Secure before leaving the enclave. This approach protects data from the OS and any malicious software, ensuring that even a privileged attacker cannot access the application’s data.
For a deeper dive into SGX and DDS Security, feel free to contact me directly.
Internet of Things Technology
- Securing DDS with Intel SGX: Part 3 – Hardened DDS Services
- Securing DDS with SGX: Building Encrypted Applications Using SCONE & Micro DDS
- Secure Your IIoT System with Custom Cryptography Libraries
- Securing the Industrial IoT: A Practical Roadmap
- Active RFID: Comprehensive Overview & Practical Use Cases
- Two Essential Strategies for IoT Security
- Securing the IoT Landscape: Key Threats and Strategic Solutions – Part 2
- IoT Security: Unpacking the Unique Threat Landscape for Connected Devices (Part 1)
- Industrial IoT Security: A Next‑Generation Blueprint – Part 2
- UID Overview Series – Part III: Shaping the Future of Unique Identification in Defense



