Ransomware Accelerates the Industrial Cybersecurity Transformation
The Colonial Pipeline ransomware incident demanded a $4.4 million ransom payment, but the real cost—lost revenue, brand erosion, and intensified regulatory oversight—ran into the tens of millions.
Following that attack, federal agencies are accelerating sweeping cybersecurity reforms, yet many industries still struggle to weave modern digital tools into legacy operations.
Data‑driven automation is spreading, but outdated manual exchanges—clipboard‑based sharing, protracted approval cycles—continue to erode efficiency and expose critical vulnerabilities.
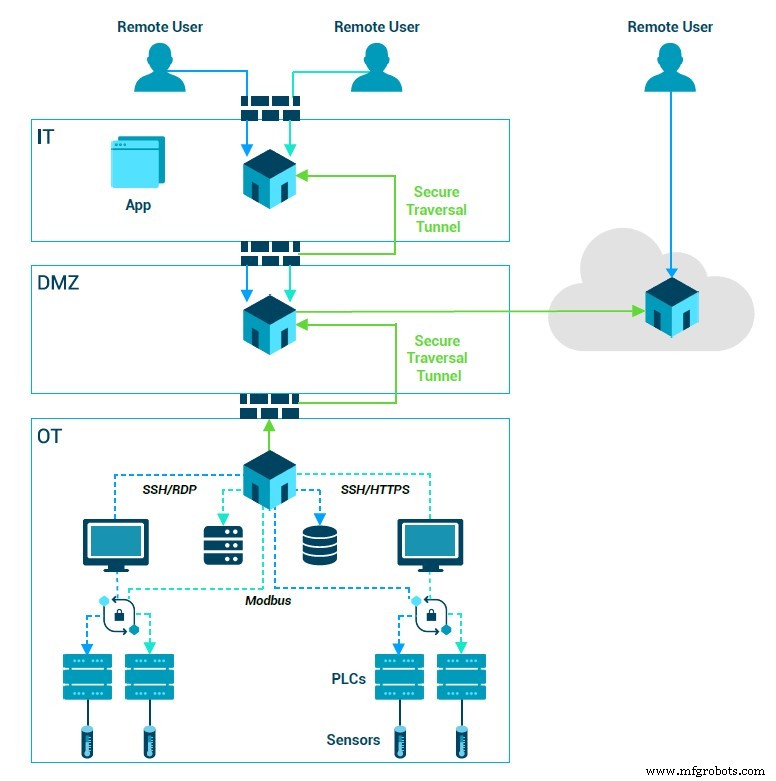
A diagram of a zero‑trust system.
With President Biden’s executive order to strengthen the nation’s cybersecurity posture, a 100‑day plan targeting the aging power grid, and the Department of Homeland Security’s new pipeline directive, industries that have not yet fully adopted modern technology are under intense pressure to upgrade their security processes and technologies. The challenge is complex and costly, but essential.
For many operators, the task feels as daunting as it is necessary. Fixing security gaps that arise when new and legacy equipment coexist requires more than a plug‑and‑play solution; it demands a fundamental shift in mindset.
Security can no longer be viewed merely as a defensive tactic. It must be the foundation for transitioning to “smart” infrastructure—a vision that has circulated for nearly a decade, yet has remained more theoretical than practical.
The vision for a smart power grid looks like this:
Electric substations would be managed by IoT devices capable of real‑time communication with administrators, partners, and customers; diverse energy assets—wind, water, solar, nuclear, and fossil fuels—would blend automatically to optimize generation and distribution; energy‑intensive sites such as data centers, large office buildings, and residential homes would deploy smart thermostats that use machine learning to reduce costs and consumption.
While these ideas are not new, a succession of high‑profile cyberattacks proved that the smart‑grid vision—and any connected infrastructure—depends on a robust cybersecurity posture.
For instance, fully automatic voltage adjustments at a substation or real‑time communication with thermostats, streetlights, and office heating systems are only possible if every interaction is secured. Otherwise, large‑scale digitization investments would introduce more cyber vulnerabilities than benefits.

Duncan Greatwood
Now that we know cybersecurity is essential for smart infrastructure, the next step is clear. Biden’s executive order calls for a departure from traditional models, urging operators to adopt zero‑trust architecture—the modern alternative to perimeter‑based security.
Zero trust is like locking every door in your home—including the fridge, pantry, and microwave—while each family member holds a unique key for each location. In contrast, a traditional approach relies on a single master key for the front and back doors.
Within this architecture, utility administrators assign each user, device, and application a distinct identity with tailored access protocols. If a cyber adversary breaches the system, the network isolates that entity and tightens controls to prevent further access.
The lack of granular control explains why incidents like the Colonial Pipeline ransomware attack can force an operation to shut down, and why almost every week a new large‑scale cyberattack cripples another critical system.
Implementing zero trust across everything—from 20‑year‑old systems with no passwords or encryption to future IoT devices with digital identities—will unlock the benefits of digital transformation. Operators will enjoy seamless remote access, efficient data sharing, and streamlined collaboration with partners, turning what was once a costly defense into a catalyst for innovation.
By mandating and incentivizing this new approach, the Biden administration is not only elevating the role of security in building smart infrastructure; it is redefining what it means to be secure. In the process, it is quietly sparking a new digital revolution within the industrial sector.
— Duncan Greatwood is chief executive officer of Xage
>> This article was originally published on our sister site, EE Times.
Internet of Things Technology
- Securing the Industrial IoT: A Practical Roadmap
- The Fourth Industrial Revolution: How Industry 4.0 Is Reshaping Manufacturing
- IoT and Industry 4.0: How the Fourth Industrial Revolution Is Shaping Manufacturing
- Designing Security into the Industrial IoT: Expert Guidelines for Protecting IIoT Systems
- Retrofitting Cybersecurity: Safeguarding Legacy Industrial Systems in the IIoT Era
- ICS Security Checklist: 8 Proven Steps to Protect Industrial Control Systems
- Protect Your Home: Secure IoT Security Cameras from Cyber Threats
- Industry 4.0 Explained: The Smart Manufacturing Revolution
- Claroty’s Cybersecurity: Why Industrial Supply Chains Demand Even Greater Protection Than Data Security
- The Fourth Industrial Revolution: How 4IR Will Reshape Manufacturing and Services



