Designing Security into the Industrial IoT: Expert Guidelines for Protecting IIoT Systems
What Is the Industrial Internet of Things?
The Industrial Internet of Things (IIoT) differs from consumer IoT by integrating operational technology—such as industrial control systems (ICS)—with enterprise IT, business workflows, and analytics. Unlike traditional OT environments, IIoT devices are widely connected to other systems and personnel, and unlike IT systems, they directly interact with the physical world via sensors and actuators, creating unique safety challenges.
Benefits and Emerging Risks
When properly implemented, IIoT enables closed‑loop systems where sensors collect data, analytics derive insights, and actuators respond in real time. This connectivity boosts efficiency, predictive maintenance, and operational visibility. However, the same openness expands the attack surface, making IIoT networks attractive targets for cyber adversaries.
DOE‑Backed Initiative for Power‑Grid Edge Security
Intel is leading a Department of Energy program focused on fortifying edge devices in the power grid. The project introduces secure gateways for legacy (brownfield) equipment and FPGA‑based upgrades for new (greenfield) devices. The goal is to shrink the cyber‑attack surface without disrupting essential energy delivery.
Five Pillars of IIoT Security
According to Sven Schrecker, Intel’s chief IoT security architect and IIC security working‑group co‑chair, security is one of five essential considerations when designing IIoT devices:
- Safety
- Reliability
- Security
- Privacy
- Resilience
Schrecker emphasizes that security policies must be co‑authored by IT and OT teams so that every device’s communication rights are clearly defined.
Building a Chain of Trust From Design to Deployment
Haydn Povey, CEO of Secure Thingz and board member of the IoT Security Foundation, outlines four organizational layers that must address security:
- CxO leadership
- Security architects
- Development engineers
- Operations managers
Development engineers translate corporate security policy into concrete design choices—such as device identity verification, secure firmware updates, and hardware attestation. Operations managers ensure that each component in the supply chain carries a unique, verifiable identity.
Challenges of a Fragmented Software Stack
Robert Martin, senior principal engineer at MITRE and IIC steering‑committee member, warns that a minor hardware change can ripple through software, producing failures that no one can attribute. He contrasts this with regulated building trades, where safety‑related modifications trigger certification.
Guidelines for Secure IIoT Design
Industry references include the IIC IoT Security Framework (with its manufacturing profile) and the NIST Cybersecurity Framework. Designers must map these frameworks onto device lifecycle requirements—identity, attack detection, recovery, remediation, and patching.
Arm’s Platform Security Architecture (PSA)
Arm’s PSA offers a three‑stage process—Analyze, Architect, Implement—to embed security from the ground up. The analysis stage involves threat modeling; Arm provides templates for asset trackers, water meters, and network cameras. Once threats are understood, designers implement measures such as immutable device identities, trusted boot, secure OTA updates, and cloud‑side verification.
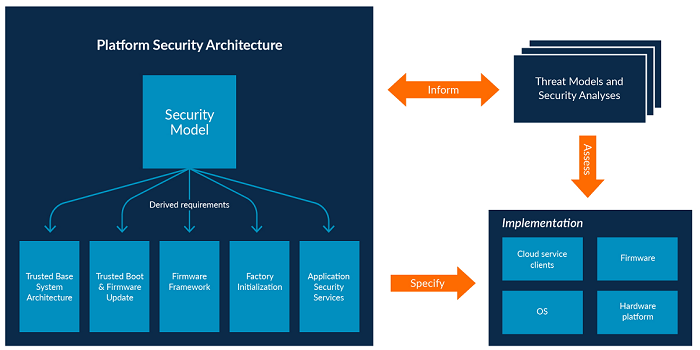 Arm’s PSA framework encourages designers to first consider threats, then shape design and implementation. (Source: Arm)
Arm’s PSA framework encourages designers to first consider threats, then shape design and implementation. (Source: Arm)
Internet of Things Technology
- Securing Industrial IoT: How Cisco Cyber Vision Completes the Security Landscape
- Securing the Industrial IoT: A Practical Roadmap
- Industrial IoT: A Practical Guide to Successful Implementation
- Two Essential Strategies for IoT Security
- Why Industrial IoT Systems Are Prime Targets for Cyberattacks—and How to Secure Them
- How Industrial IoT Sensors Drive Modern Factory Efficiency
- Infographic: Mastering the Industrial IoT Maturity Journey
- Securing Your IoT Ecosystem: Expert Strategies to Counter Ransomware and Cyber Threats
- Industrial IoT Security: A Next‑Generation Blueprint – Part 2
- Is Security the Biggest Threat to Industrial IoT?



