Six Proven Steps to Secure Embedded IoT Systems
 Mark Pitchford of LDRA
Mark Pitchford of LDRA
Security remains a paramount concern for the vast array of embedded devices powering the Internet of Things—from power grids and automotive systems to medical devices and everyday appliances. If compromised, these systems can expose critical infrastructure, personal data, and public safety to significant risk, says Mark Pitchford of LDRA.
Prevention is the most cost‑effective strategy, echoing the “shift left” philosophy that moves security from the end of the process to the very beginning. By embedding security into the design and development stages, teams can reduce vulnerabilities early and avoid expensive rework later.
Here are six industry‑backed practices that deliver high‑quality, secure embedded software.
1. Build security into the software development life cycle
Traditional secure‑code checks are often reactive—code is written to broad guidelines and then inspected for flaws. Whether using Agile or a more classic waterfall approach, the key is to treat security requirements as first‑class citizens throughout the entire lifecycle. Integrating threat modeling, secure design patterns, and code‑level security controls from the outset ensures a more robust end product.
In both linear and iterative models, security must be woven into each phase—requirements, design, implementation, and testing—rather than treated as a post‑hoc add‑on.
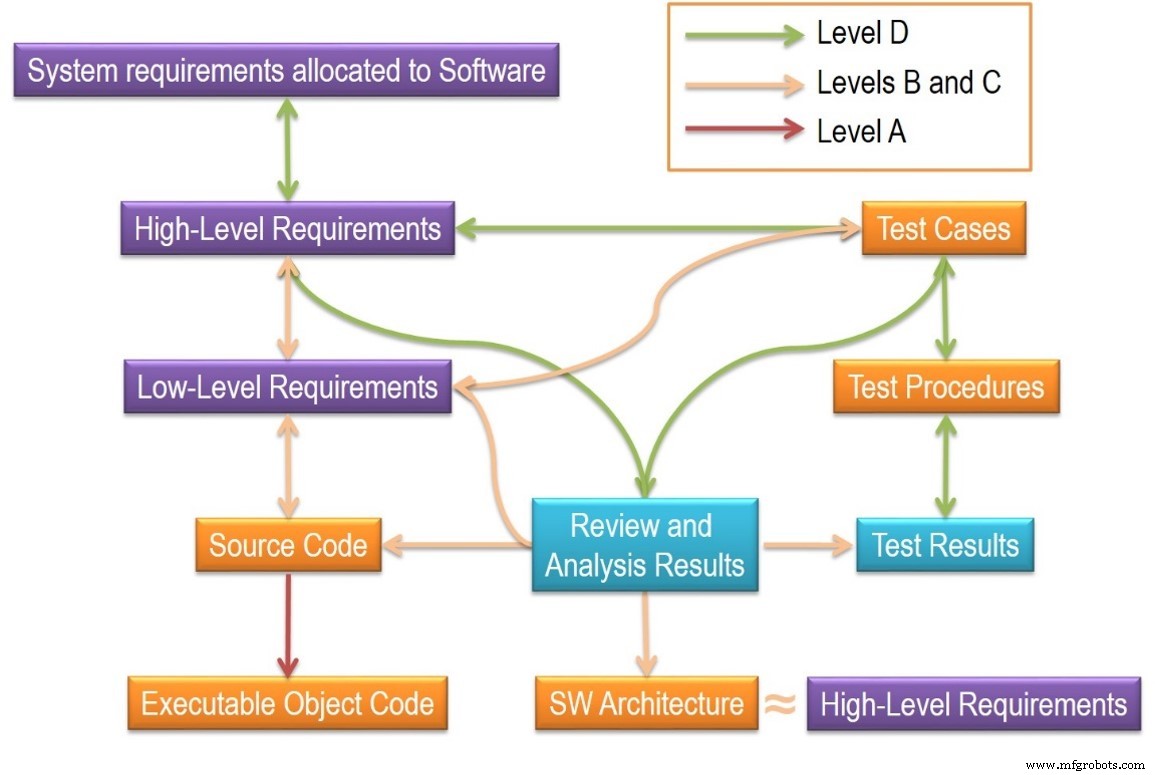
2. Ensure bidirectional traceability
Functional‑safety standards mandate evidence of bidirectional traceability across all development phases. This same rigor applies to security: traceability guarantees that every requirement has a corresponding design element, code block, and test case, and that changes propagate correctly. Automated tools can regenerate compliance artifacts on demand, simplifying audits and reducing the risk of hidden backdoors.
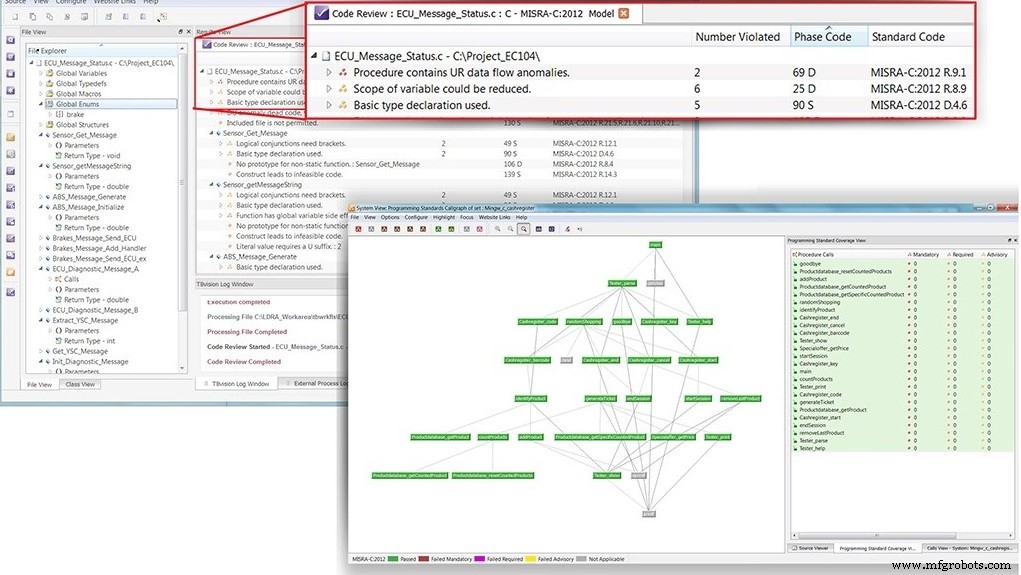
3. Choose a secure language subset
In C and C++, roughly 80 % of defects stem from misuse of a small portion of language features. By restricting the language to a vetted subset—such as MISRA C or CERT C—developers can eliminate many common vulnerabilities at compile time. While manual enforcement is laborious, integrating static analyzers into the build pipeline automates compliance and preserves productivity.
4. Use a security‑focused process standard
Although security standards are still evolving, industry leaders are rapidly adopting them. For example, ISO/SAE 21434 “Road Vehicles Cybersecurity Engineering” provides detailed guidance for automotive connectivity, complementing the higher‑level SAE J3061. Adopting such standards ensures a structured, repeatable approach to threat mitigation.
5. Automate as much as possible
Automation at every stage—from requirement capture in tools like IBM Rational DOORS to model‑based testing—reduces human error and accelerates feedback loops. Static analysis engines verify compliance with coding and safety standards, while dynamic analysis and penetration testing confirm that the software behaves securely under attack.
6. Select a secure software foundation
Secure embedded software must run on a trustworthy platform. Domain separation isolates the application from other components, limiting the blast radius of a compromise. Integrated test harnesses that span requirements to documentation allow developers to validate security throughout the build environment.
Adopting these six processes provides a cohesive strategy for building embedded IoT systems that are safe, secure, and reliable.
The author is Mark Pitchford of LDRA.
For more information click here: Learn more about embedded security
Internet of Things Technology
- Securing Industrial IoT: How Cisco Cyber Vision Completes the Security Landscape
- Securing the Industrial IoT: A Practical Roadmap
- Two Essential Strategies for IoT Security
- Securing IoT: Protecting Your Network from Cyber Attacks
- Securing Your IoT Ecosystem: Expert Strategies to Counter Ransomware and Cyber Threats
- Protecting IoT Devices with Deception Technology
- Securing the IoT from Hardware to Application: A Layer‑by‑Layer Blueprint
- How to Hire the Ideal CISO for an IoT-Driven Enterprise
- Six Proven Steps to Secure Your Industrial IoT Platform
- IoT Security Demystified: Protecting Your Connected Devices



