Dell Survey Reveals Widespread Security Lapses in Large Enterprises
Dell recently conducted a survey of 2,608 global professionals working for enterprises with 250 or more employees. The findings are startling and have implications for any organization that handles private or corporate data.
Today, we entrust corporations with our most sensitive information. Whether it’s Google safeguarding our search queries, cloud services monitoring our health data, or e‑commerce sites protecting our finances, the stakes are high.
Phishing Employees for Company Information
Data security is only as strong as the processes that protect it. Many high‑profile breaches stem from phishing attacks that trick employees into revealing credentials or confidential data. Verizon’s 2023 report highlighted phishing as a top threat to enterprise security.
Phishing is a form of social engineering where an attacker convinces an employee to disclose information they should not. Common tactics include:
- Impersonating a trusted vendor or IT technician over the phone to request passwords.
- Sending emails with spoofed links that mimic legitimate portals, prompting users to enter credentials.
See also: Will these Chinese satellites provide hackproof data security?
What Dell’s Survey Discovered
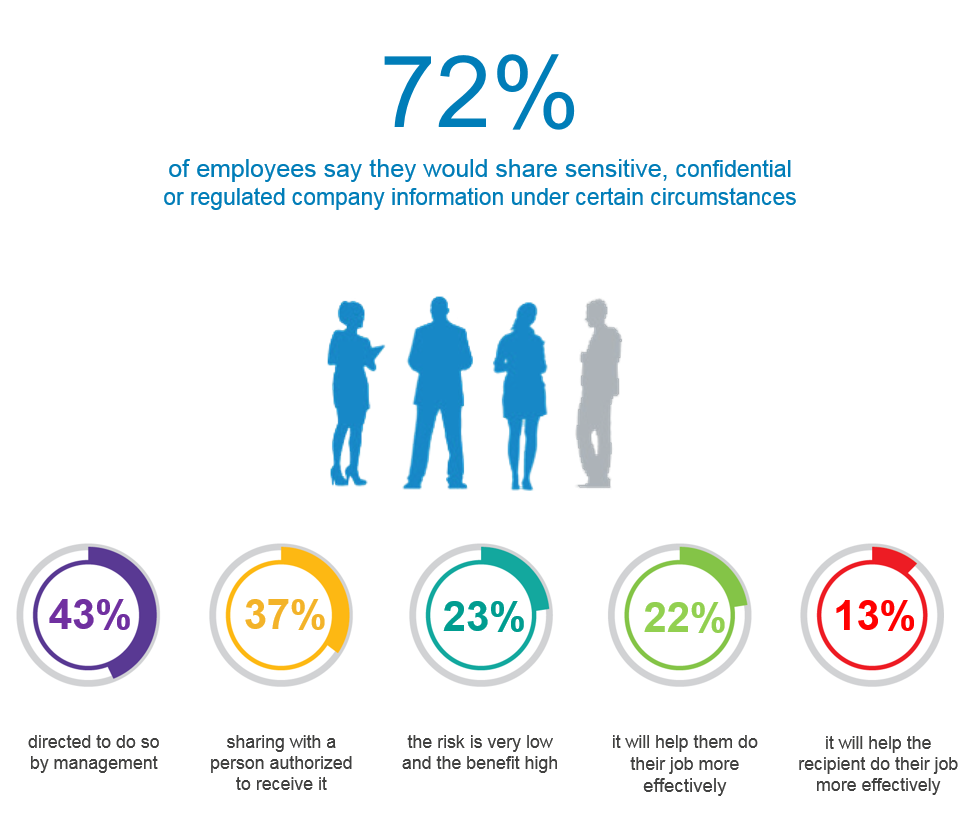
In Dell’s End‑User Security Survey, 72% of respondents admitted they would share sensitive, confidential, or regulated company data under certain circumstances. The reasons varied:
- Being directed to do so by management – 43%
- Sharing with an authorized recipient – 37%
- Low perceived risk and high perceived benefit – 23%
- Enhancing their own job performance – 22%
- Improving the recipient’s job performance – 13%
The data reveal a general lack of caution. Employees often take shortcuts when they believe it will help them work more efficiently, viewing stringent security protocols as obstacles.
Unsafe Practices Are Common
Unsafe data‑sharing habits extend beyond direct disclosure. 45% of participants admitted to engaging in behaviors that many organizations would prohibit.
- 46% connected to public Wi‑Fi while accessing confidential information, even when VPNs or secure remote access were available.
- 49% used personal email accounts for work-related communications – a practice that has exposed several high‑profile U.S. government officials to data‑breach risk.
For instance, in January, it was revealed that the official Twitter account of the U.S. President was protected by a Gmail address. Such incidents underscore the risks of using personal email for sensitive communications.
These findings illustrate how well‑meaning employees can inadvertently compromise corporate security. The hope is that insights like these will motivate IT leaders and business executives to refine security protocols and foster a culture of compliance.
Internet of Things Technology
- 5 Essential Security Practices for Protecting Data with AWS Backup
- From Field Sensors to Strategic Insights: Leveraging IIoT Data with IXON Cloud
- Harnessing Data Visualization for IoT and AI Insights
- Tableau: Turning Raw Data into Strategic Insight
- Master Enterprise Data Management in 7 Proven Steps
- ERP Systems: The Backbone of Industry 4.0 Data Integration
- Mastering Data Migration: Proven Best Practices for Seamless Platform Transitions
- Modernize Your Maintenance Strategy with Proven CMMS Best Practices
- 2022 Cybersecurity Landscape: Scope and Impact on IT
- Ensuring Data Security in the Cloud: Protecting Your Information with Confidence



