Scaling IoT Networks: Overcoming the Scalability Challenge with Cisco DNA Center Automation
The Internet of Things (IoT) presents a range of challenges for network engineers. In my previous post, I explored how Cisco addresses the paramount issue of security. Today, we tackle the next hurdle: scalability.
As illustrated below, tens of billions of devices are slated to go online over the next few years, raising significant scalability concerns for IoT deployments.
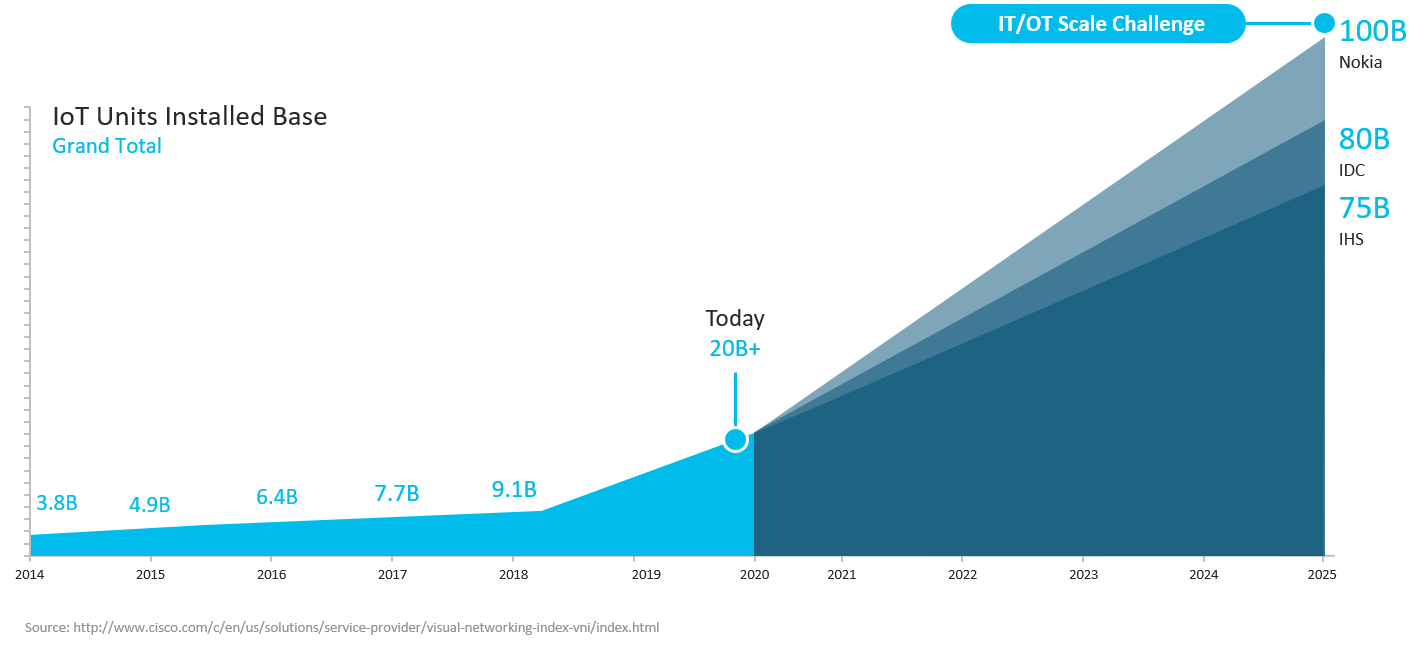
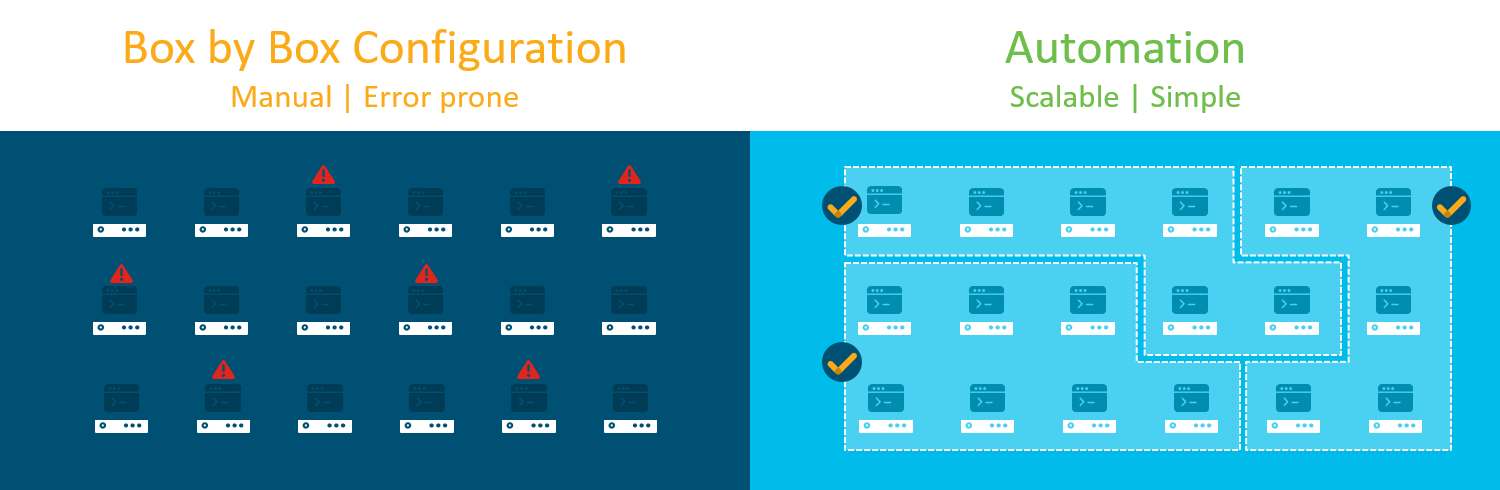
How can organizations scale security and network policies to accommodate such a massive device fleet? Configuring each IoT device as we do with traditional network gear—one at a time—simply cannot meet the scalability demands of modern IoT environments. Manual, box‑by‑box configuration is slow and error‑prone.
The solution lies in automation. Deploying policies at scale through automation accelerates provisioning and simplifies software management. This is achieved through software‑defined access.
Scaling IoT with Cisco DNA Center
Suppose you need to apply a network policy to your IoT devices. Each device should reside on its own VLAN, isolated from the rest of the enterprise network to prevent lateral movement by attackers.
With Cisco DNA Center, creating a new virtual network is as straightforward as naming the network and selecting the user, device, or application groups that belong on it—known as Scalable Groups. By dragging and dropping the relevant icons and clicking save, the platform automatically segments the IoT devices so they can only communicate with the devices specified in the virtual network. There’s no need to manually configure VLANs, DHCP scopes, or ACLs; the operator can apply policies without deep networking expertise.
The Scalable Group Tag (SGT) is the key enabler. An SGT is a logical policy object that identifies the endpoints, users, or applications to which a policy applies. SGTs support IP‑address‑independent Group‑Based Policies, allowing operators to apply rules to entire groups instead of individual IP addresses—a method that becomes unwieldy at scale.
This approach mirrors the process used for traditional enterprise devices. However, IoT endpoints typically lack the computational power and hardware resources of data‑center switches, being smaller, lighter, and more power‑efficient.
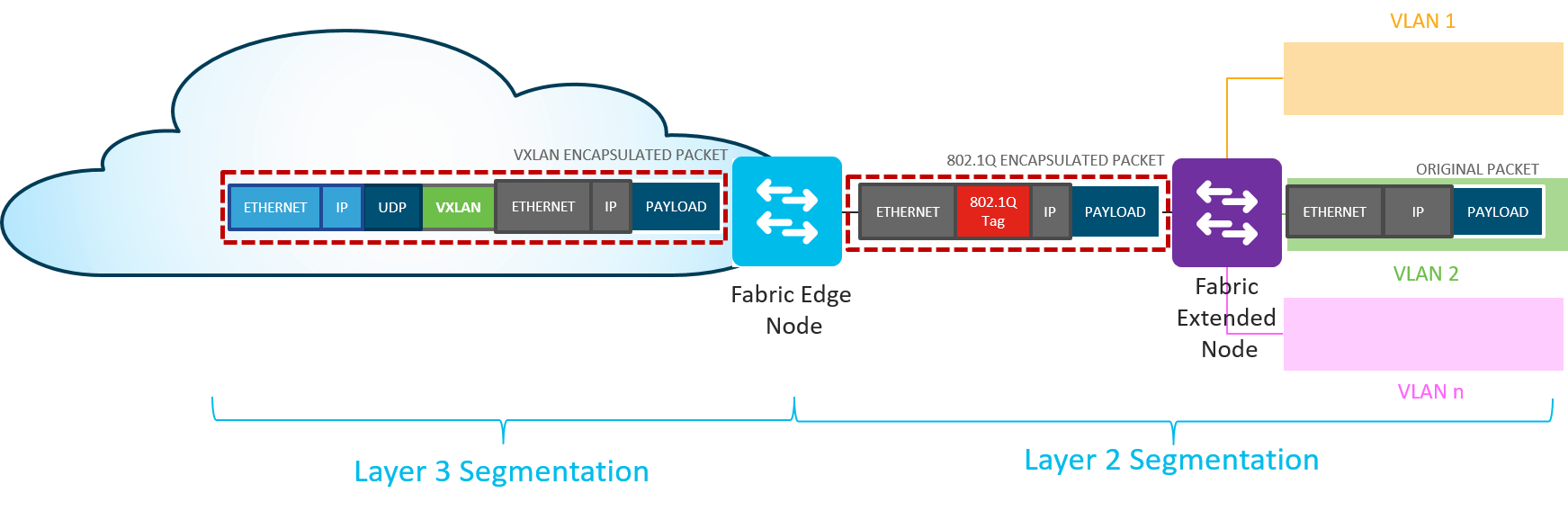
To reconcile the need for segmentation with the hardware constraints of IoT, Cisco introduced Software‑Defined Access Extended Nodes. These nodes enable the following workflow:
- The extended node connects to a single Edge node via an 802.1Q trunk port, supporting one or multiple VLANs with static assignment.
- Switch ports on the extended node are statically assigned to an IP pool managed in Cisco DNA Center.
- SGT mapping is performed through pool‑to‑group mapping in Cisco DNA Center on the connected Edge node.
- Traffic policy enforcement based on Scalable Group ACLs is executed at the Edge node.
Scaling traditional enterprise networks was challenging when operators had to configure each device manually. Doing so for billions of IoT endpoints is nearly impossible. Cisco’s software‑defined access and automation capabilities solve this problem, enabling the same management interface used for enterprise devices to govern IoT deployments efficiently and effectively.
Interested in learning more? Watch our on‑demand webinar, "Cisco IoT: Drive Transformation in the Public Safety, Oil and Gas, and Manufacturing Sectors." Be sure to return to the Cisco IoT blog for additional insights into the top challenges facing enterprise IoT, including security.
Internet of Things Technology
- Industrial IoT Security Lessons from the Mirai DDoS Attack
- IoT Security: The Biggest Challenge and How to Overcome It
- Reviving Maintenance: From Obsolescence to Sustainable Excellence
- 3D Printing Today and Tomorrow: What You Can Create Now and What the Future Holds
- IoT Security Essentials: Protecting Your Devices from Modern Cyber Threats
- IoT & Home Automation: Shaping the Smart Living of Tomorrow
- How Cold Chains Reveal the Secrets of IoT Power Management
- SolarWinds Breach Reveals IoT and Supply-Chain Security Vulnerabilities
- Key Causes of Hydraulic Pump Failure and How to Prevent Them
- Refrigerant Dryers Explained: Moisture Control & Environmental Benefits



