Industrial IoT Security Lessons from the Mirai DDoS Attack

 The Mirai DDoS attack that unfolded last Friday exposed a fundamental weakness in today’s IoT deployments. Though it targeted consumer devices, the same vulnerabilities resonate in industrial environments. The botnet leveraged tens of millions of IP addresses, exploiting manufacturer‑set default passwords that are notoriously easy to guess. How many industrial operators have encountered the same default‑password dilemma? More importantly, how many have ever audited their devices to confirm a password change? The numbers suggest the latter is a rare practice.
The Mirai DDoS attack that unfolded last Friday exposed a fundamental weakness in today’s IoT deployments. Though it targeted consumer devices, the same vulnerabilities resonate in industrial environments. The botnet leveraged tens of millions of IP addresses, exploiting manufacturer‑set default passwords that are notoriously easy to guess. How many industrial operators have encountered the same default‑password dilemma? More importantly, how many have ever audited their devices to confirm a password change? The numbers suggest the latter is a rare practice.
While it may seem that industrial networks are insulated from such large‑scale assaults, the underlying attack strategy is directly applicable. By compromising one or many peripheral devices, an adversary can launch secondary attacks against mission‑critical assets or entire networks. Industrial defenders must therefore anticipate and mitigate this “lateral attack” vector.
- The devices are deployed in remote, hard‑to‑manage sites where software updates are sporadic or absent.
- They operate autonomously with minimal operator oversight; administrators often set them once and forget them.
- They connect to broader networks and share data, increasing exposure.
- Compromise vectors are typically simple and low‑cost.
- Network transport security is often insufficient, leaving data vulnerable.
- Because compromised devices are merely stepping stones, manufacturers have little incentive to invest in robust security.
Do these characteristics mirror your industrial environment? They do, and history confirms it. The 2015 attack on Ukraine’s electricity distribution SCADA system demonstrated that reliance on isolation and anonymity is no longer enough. As more industrial devices integrate with the internet and private networks, the attack surface widens. Threats can also enter via physical intrusion (e.g., Stuxnet) or by exploiting poorly designed software. The assumption that a network can be perfectly guarded is unrealistic; instead, we must design for the presence of internal adversaries.
The first line of defense is device hardening. Industries need to adopt comprehensive signing and security practices that cover hardware chips, operating systems, libraries, and applications. Secure boot, chain‑of‑trust mechanisms, and signed firmware are essential prerequisites for any industrial deployment.
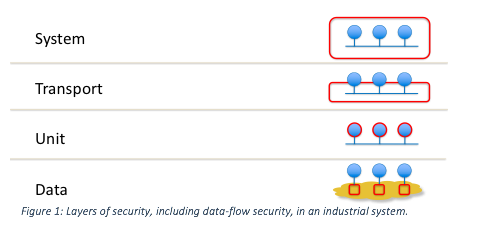
Even with robust device security, we cannot assume all network participants remain uncompromised. Industrial data is mission‑critical and must be protected at every layer.
Enter the OMG Secure DDS standard and RTI Connext® DDS Secure—solutions that embed security directly into the data‑distribution infrastructure. RTI Connext DDS, built on the OMG Secure DDS standard, offers:
- Discovery authentication
- Data‑centric access control
- Cryptographic protection
- Tagging & logging
- Non‑repudiation
- Secure multicast
These capabilities are transport‑agnostic and plug‑in‑ready, allowing organizations to replace underlying security libraries via standard APIs without altering application logic.
Key distinctions of Secure DDS compared to traditional network security tools:
- Security is integral to the infrastructure and reflected in Quality‑of‑Service metrics.
- It supports fine‑grained, data‑topic‑level access control—what we call data‑flow security.
- It enables a configurable mix of encryption, authentication, and access control tailored to each data topic.
- Configuration drives security; application developers can focus on functionality while architects manage security policies.
Secure DDS delivers a fundamentally different paradigm: security baked into the fabric of the network from day one. This leads to simpler deployment, higher performance, and greater resilience. Our customers, who rely on DDS Secure for some of the most critical industrial applications, attest to its effectiveness.
Tools are already available; the next step is to adopt them and chart a migration path toward this secure model. Learn more about RTI Connext DDS Secure here and contact us to explore how RTI’s solutions can safeguard your IIoT environment.
[i] https://www.techrepublic.com/article/dyn-ddos-attack-5-takeaways-on-what-we-know-and-why-it-matters/
[ii] https://www.computerworld.com/article/3134746/security/fridays-iot-based-ddos-attack-has-security-experts-worried.html
Internet of Things Technology
- IoT Security: The Biggest Challenge and How to Overcome It
- Scaling IoT Networks: Overcoming the Scalability Challenge with Cisco DNA Center Automation
- Securing the Industrial IoT: A Practical Roadmap
- AirFinder Bluetooth LE & XLE: Top IoT Solutions for Industrial Asset Tracking
- Designing Security into the Industrial IoT: Expert Guidelines for Protecting IIoT Systems
- IoT Security Lessons from Recent Breaches: Protecting Your Enterprise
- Securing the IoT from Hardware to Application: A Layer‑by‑Layer Blueprint
- How COVID‑19 Shaped Healthcare IoT Cybersecurity: Lessons from the First Wave
- Understanding the WPA2 Vulnerability and Its Impact on IoT Devices
- How 5G Adoption Enhances IoT Security: What You Need to Know



