Arcane Vulnerability Disclosure Programs Leave IoT and Industrial Control Systems Exposed
Most product vulnerabilities today are found by independent researchers rather than the vendors themselves, creating a patchwork of exposure across the industry.
Internet of Things (IoT) and Industrial Control System (ICS) devices are becoming a hotbed for high‑severity flaws. Claroty’s latest ICS Risk & Vulnerability Report notes that more than 600 critical or high‑severity issues were disclosed in the first half of this year alone. Nearly a quarter of these flaws have no fix or can only be partially remedied, and many can be exploited remotely to render components inoperable.
A recent example is the BadAlloc cluster discovered in real‑time operating systems (RTOS) and associated libraries from multiple suppliers. Attackers can leverage these vulnerabilities for denial‑of‑service or remote code execution, threatening the entire software supply chain.
click for full size image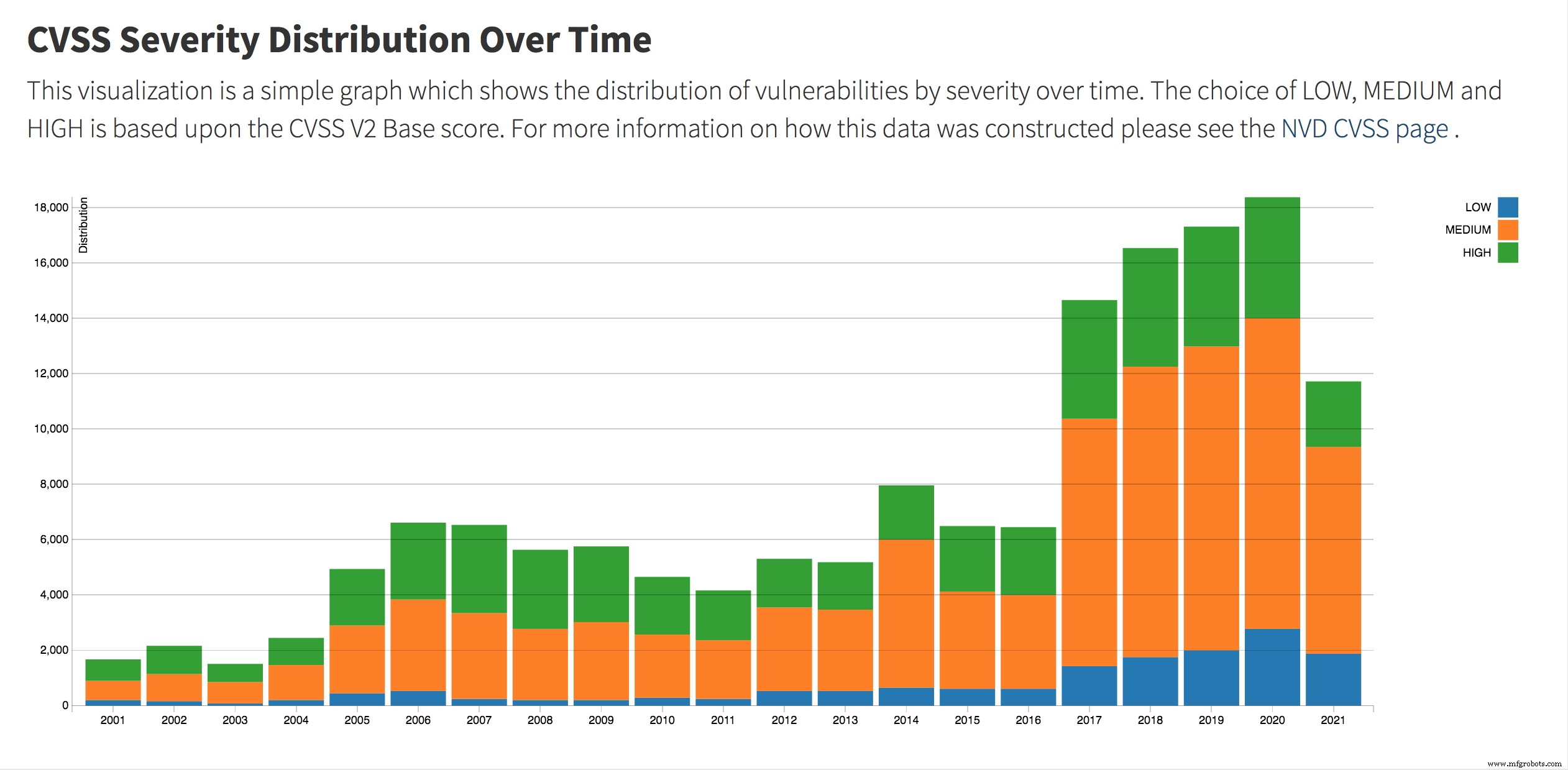
(Source: National Institute of Standards and Technology)
Millions of IoT, operational technology (OT) devices—including vehicles and medical equipment—are potentially at risk. Yet many OEMs and asset owners were unaware of these flaws until Microsoft disclosed them in April.
Vulnerability disclosure programs (VDPs) were created to bridge this gap. As Bugcrowd’s 2021 Ultimate Guide explains, VDPs “provide a mechanism for identifying and remediating vulnerabilities discovered outside the typical software development cycle.” They are typically run by federal agencies, industry groups, or large vendors.
No Consistency Across Programs
In September 2020, the Cybersecurity and Infrastructure Security Agency (CISA) issued a binding directive requiring federal agencies to publish their vulnerability disclosure policies—an initiative that has led to a proliferation of disparate VDPs. CISA’s VDP Platform, provided by Bugcrowd and EnDyna, serves civilian federal agencies as a centralized hub for researchers to report security issues on agency websites.

Ron Brash
However, most VDPs focus on product vulnerabilities rather than process or configuration weaknesses, and there is little alignment among them. "These programs are all over the map: even U.S. federal agencies do their own thing," says Ron Brash, director of cyber security insights at Verve Industrial Protection, in EE Times. "None of them are set up for maximum efficiency." Even respected frameworks such as NIST and ISO/IEC suffer from inconsistencies in reporting, enforcement, and remediation workflows.
Brash also highlights a transparency gap. Federal agencies do not own the commercial off‑the‑shelf (COTS) products they procure, acting instead as intermediaries. "The people policing these products lack deep technical knowledge, budget constraints, and approval bottlenecks," he notes, making it difficult to compel vendors to issue fixes or enforce compliance.
Ownership ambiguity extends to advisories themselves. Large vendors often claim responsibility, but fragmented business units and multi‑vendor product stacks further dilute accountability. "Since each product can combine multiple products, the number of vendors multiplies even more," Brash observes.
Limitations of the CVE Reporting System
CISA hosts two central U.S. VDPs: the National Vulnerability Database (NVD) at NIST and the Common Vulnerabilities and Exposures (CVE) program run by MITRE, both of which catalog publicly known vulnerabilities. CISA also publishes the ICS‑CERT advisories, detailing exploits and operational issues.
"Even if we ignore the disclosure process and research aspects, the CVE system is arcane and complex," Brash argues. "Asset owners often lack the expertise to interpret OT/ICS advisories, leading to paralysis in the face of overwhelming data." The complexity is evident in Brash’s YouTube presentation, a primer on navigating CVE entries.
Moreover, the CVE database does not capture every vulnerability. According to Risk Based Security, 2,158 vulnerabilities were published in July, 670 of which lacked a CVE identifier.
John Jackson, founder of Sakura Samurai, notes that “CVE coverage focuses on widely used software; a flaw unique to a single company’s logic or server may never appear in the database.”
Federal VDPs primarily target federal agencies, with limited resources for commercial entities. While some industries have dedicated regulators—such as the North American Electric Reliability Corporation (NERC) for utilities—these frameworks can shift with policy changes.
“Some open‑source projects manage vulnerability disclosures effectively,” Brash says. “Certain parts of the Linux kernel have robust processes, while others lag. Even within the broader Linux ecosystem, security practices vary widely.”
Reporting and Disclosure Challenges
The lack of standardization in reporting places researchers at a disadvantage, especially when legal risks loom under the Computer Fraud and Abuse Act (CFAA). "Many VDPs require researchers to refrain from discussing findings, offer no compensation, and are overseen by non‑security personnel," Jackson cautions. "This environment hampers collaboration and weakens the overall security posture."
A 2016 NTIA report found that 92% of researchers engage in coordinated disclosure, yet 60% cite legal threats as a deterrent, and only 15% expect a bounty—though 70% anticipate regular communication about the bug. Bugcrowd’s 2021 guide reports that 87% of organizations with VDPs received a critical vulnerability through the program, but only 79% actually compensate researchers for impactful findings.
Given the intricacies of embedded, IoT, and industrial product vulnerabilities, Brash calls for a standardized disclosure framework. He envisions a registry—akin to automotive recall systems—for embedded IoT devices, ensuring OEMs and system integrators inform asset owners promptly. "With a clear record of vulnerabilities, owners can choose to accept risk, apply patches, or replace equipment, mirroring the car recall process," he asserts.
>> This article was originally published on our sister site, EE Times.
Internet of Things Technology
- Two Essential Strategies for IoT Security
- Arcane Vulnerability Disclosure Programs Leave IoT and Industrial Control Systems Exposed
- Why Industrial IoT Systems Are Prime Targets for Cyberattacks—and How to Secure Them
- Securing the Industrial Internet of Things: Strategies, Standards, and the Chain of Trust
- Essential Hardware Security Vulnerabilities Every Engineer Must Understand
- Supply Chain Vulnerabilities Threaten Industrial IoT Security
- Understanding the WPA2 Vulnerability and Its Impact on IoT Devices
- 2022 Cyber Asset Survey Reveals Ongoing Vulnerabilities in Cloud
- SimpliSafe Security System Hack Exposes IoT Vulnerability: $2 Wireless Emitter Hacks Door Sensors
- Essential Cloud Security Strategies to Minimize Risks, Threats, and Vulnerabilities



