IoT Security: Understanding and Defending Against Mirai, Stuxnet, and Other Cyber Attacks
 Editor’s Note: Securing the Internet of Things is essential not only for protecting data streams and software within each IoT application, but also for safeguarding enterprise resources that depend on those applications. IoT security is a complex challenge that demands a systematic approach to identifying threats and implementing effective mitigation strategies.
Editor’s Note: Securing the Internet of Things is essential not only for protecting data streams and software within each IoT application, but also for safeguarding enterprise resources that depend on those applications. IoT security is a complex challenge that demands a systematic approach to identifying threats and implementing effective mitigation strategies.
Adapted from Internet of Things for Architects, by Perry Lea.
Chapter 12. IoT Security
By Perry Lea
Anatomy of IoT Cyber Attacks
While the field of cybersecurity is vast, this chapter focuses on three representative IoT-based attack vectors that illustrate the breadth of threats across hardware, networking, protocols, cloud components, and operating systems. Understanding these attack modalities enables architects to design resilient defenses.
- Mirai: The most damaging distributed denial‑of‑service (DDoS) campaign in history, originating from insecure IoT devices worldwide.
- Stuxnet: A nation‑state cyber weapon that targeted industrial SCADA PLCs, causing irreversible damage to Iran’s nuclear centrifuges.
- Chain Reaction: A research proof‑of‑concept that demonstrates how a simple LED light can compromise PAN‑level networks without internet connectivity.
By dissecting these threats, designers can select appropriate technologies and processes to preempt similar incidents.
Mirai
Mirai is a malware that first appeared in August 2016, infecting Linux‑based IoT devices and forming a botnet capable of launching massive DDoS attacks. High‑profile victims included the security blog Krebs on Security, DNS provider Dyn, and telecom operator Lonestar Cell, among others. The botnet’s impact was felt across a spectrum of services—Sony PlayStation, Amazon, GitHub, Netflix, PayPal, Reddit, and Twitter—when Dyn was overwhelmed.
At its peak, Mirai infected approximately 600,000 devices, predominantly IP cameras, DVRs, routers, VOIP phones, printers, and set‑top boxes. The malware was distributed in three stages:
- Discovery: Mirai performed an asynchronous TCP SYN scan for SSH/Telnet on ports 23 and 2323, respecting a blacklist of 3.4 million IP addresses (e.g., U.S. Postal Service, Hewlett Packard, Department of Defense). The scan rate averaged 250 bytes/s, a modest speed suitable for constrained IoT devices.
- Credential Brute‑Force: The malware attempted 62 username/password combinations. Successful logins were reported to a central command‑and‑control (C2) server.
- Infection & Persistence: A loader binary identified the target’s architecture (32‑bit ARM, MIPS, or X86) and deployed device‑specific payloads. Competing processes on ports 22/23 were terminated, and the loader was obfuscated and deleted to avoid detection. The bot remained dormant until a C2 command was received.
Mirai’s DDoS tactics included SYN floods, GRE IP network floods, STOMP floods, and DNS floods. Over five months, the botnet executed 15,194 attack commands against 5,042 internet sites, generating peaks of 623 Gbps—recording the most powerful DDoS attack to date.
click for larger image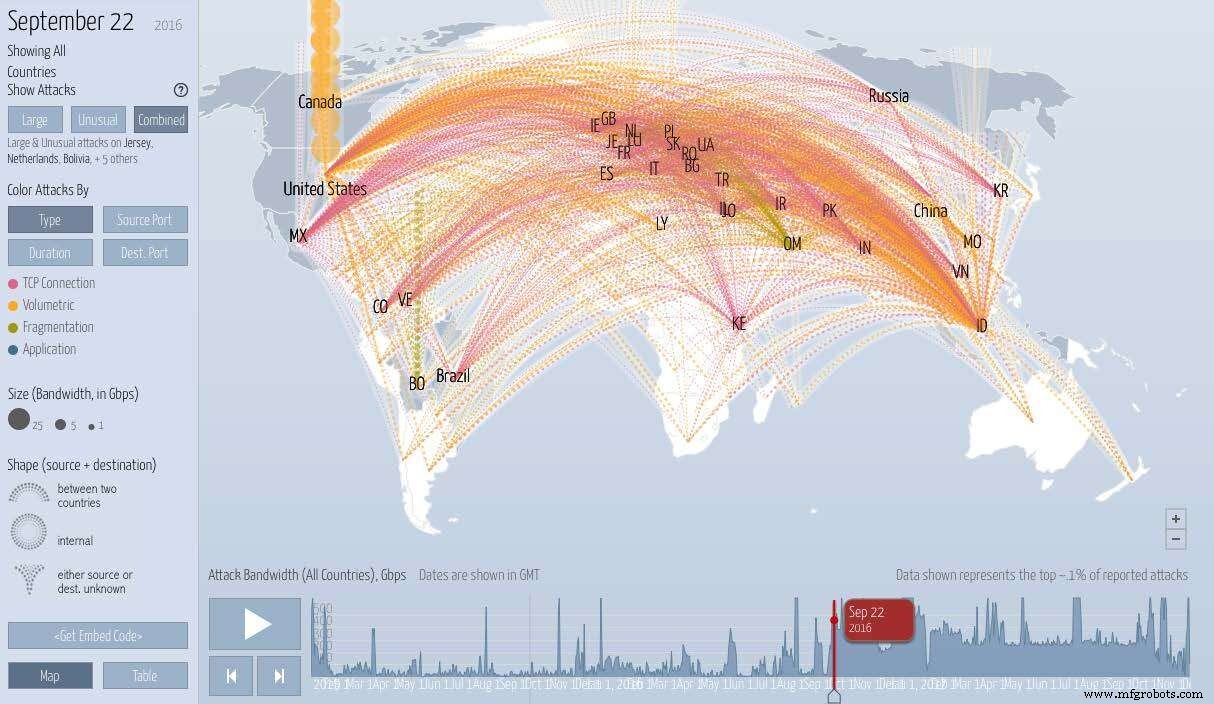
A view of the Mirai DDoS attack on the Krebs on Security website; courtesy of www.digitalattackmap.com
Stuxnet
Stuxnet represents the first documented cyber weapon engineered to permanently damage another nation’s industrial infrastructure. The worm targeted Siemens S7‑300 PLCs controlling critical SCADA systems. Its payload was engineered to alter the rotational speed of motors in industrial equipment—specifically pumps and uranium‑enrichment centrifuges—by modifying the slave variable frequency drives operating at 807 Hz and 1210 Hz.
Stuxnet’s sophistication lay in its multi‑stage zero‑day exploits, rootkit capabilities, and the precision with which it reprogrammed PLC logic, causing catastrophic failures without alerting operators.
Continue to page two of this article >>
Internet of Things Technology
- Securing the Industrial IoT: A Practical Roadmap
- Four Critical IoT Security Threats in 2015 — What Developers Need to Know
- Two Essential Strategies for IoT Security
- IoT Security – A Practical Guide from Perry Lea
- Securing IoT: Protecting Your Network from Cyber Attacks
- IoT Security – Who Holds the Responsibility?
- IoT Security: Overcoming Deployment Barriers
- Future-Proofing IoT Security: Expert Strategies for a Safer Connected World
- IoT Device Adoption Fuels Rising Cybersecurity Threats: What Governments Must Do
- IoT Security Essentials: Protecting Your Devices from Modern Cyber Threats



