Securing Smart Meter Lifecycles: Six Proven Strategies for Privacy and Resilience
The Internet of Things is expanding at an unprecedented pace, driving the projection of a trillion connected devices by 2035—far surpassing today’s data volumes. Smart meters are among the fastest‑growing IoT segments. iHS Markit estimates that Advanced Metering Infrastructure spend will reach $13 billion in 2023, up from $9 billion in 2018. Utilities are reaping the rewards of automated meter reading, precise billing, and remote control, all while reducing resource consumption.
However, this explosive expansion widens the attack surface for cybercriminals targeting critical infrastructure or pilfering sensitive data. In December 2016, the ‘Crash Override’ malware commandeered Ukraine’s power grid, disabling 30 substations and plunging Kiev’s electricity supply to one‑fifth of its capacity.
Smart‑meter security threats manifest across the device’s entire operational life. Utilities must anticipate diverse attack vectors—from side‑channel exploits like Correlation Power Analysis that reveal credentials, to data breaches at the edge or in the cloud. Enforcing end‑to‑end security, including OTA firmware updates, is essential. So, how can utilities guarantee that smart‑meter deployments protect every stakeholder?
Meter‑resident data—often containing Personally Identifiable Information—has direct privacy implications. Utilities use this data to forecast demand, deploy demand response, and recommend consumption patterns, but it must be handled responsibly and in compliance with regulations such as the EU’s General Data Protection Regulation (GDPR). A trusted data foundation, rooted in device‑level security, authentication, and encryption at rest and in transit, is therefore mandatory.
Six ways an IoT platform enables secure and private smart meters
Achieving robust smart‑meter security demands a holistic lifecycle strategy—from factory production through onboarding and ongoing operations (see Figure 1). The Arm Pelion IoT platform embeds the essential device‑management and access‑control features to support this journey. Below, we outline six key ways the platform safeguards privacy throughout the meter’s lifecycle.
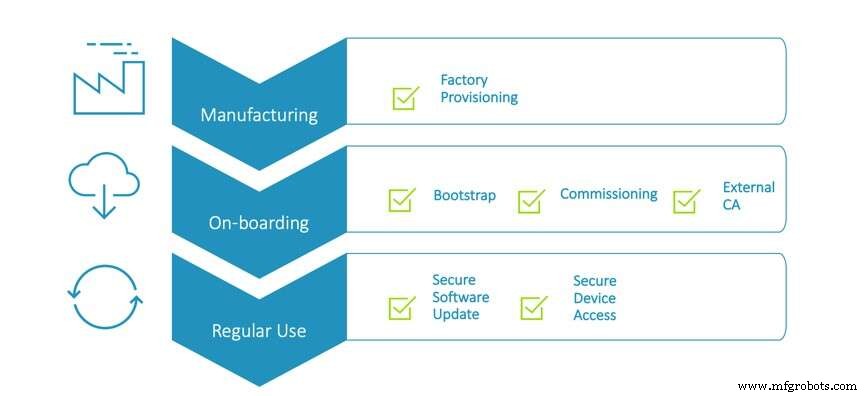
Figure 1: An example of a secure device lifecycle. (Source: Arm Pelion IoT platform)
1. Establishing a Root of Trust for Millions of Meters During Factory Provisioning
Manufacturing plants must juggle high throughput with robust resilience, ensuring every meter is inherently trustworthy and starts its field life on a secure footing.
The production facilities tasked with manufacturing smart meters need to balance scalability with resilience that will ensure a device is trusted, offering a secure foundation for the meter’s life in the field. Injecting credentials onto a single device can mitigate this risk, but the ability to scale this process to the millions of devices is key in maintaining the balance between efficiency and security. The matter of trusting a factory becomes more of a concern when you consider that utility companies are not manufacturers themselves and often outsource production and trust to OEMs. So how do we make a third‑party factory ‘trusted’?
Trust is instilled by administering certifying authorities that cross‑reference the IoT platform, bootstrap, and lightweight M2M (LwM2M) servers. A range of tools provided by the IoT platform provider offers a linear process for the configuration of the certificate authority (CA) that ensures only meters that possess a certificate signed by a CA and a public key can establish a connection between the device and its device manager.
click for larger image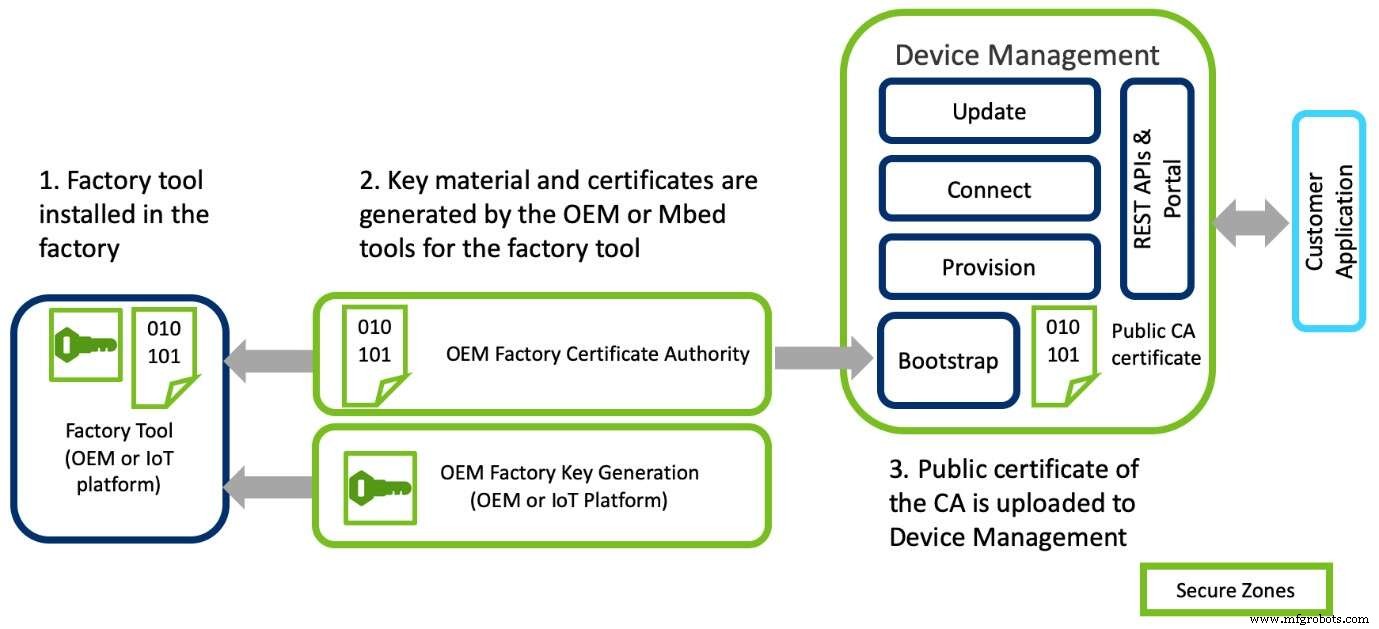
Figure 2: An example of secure factory provisioning (Source: Arm Pelion IoT platform)
Once the CA is configured and linked to the manufacturer’s individual account the factory line is ready to mass‑provision devices. This five‑stage process involves:
- Injecting the software image
- Generating device keys, certificates and configuration parameters for the device
- Using a factory tool to inject the generated keys, certificates and configuration parameters into the device on the manufacturing line
- Using a key configuration manager and factory configurator client (FCC) APIs in the device to validate the information
- Finalizing the provisioning process and blocking the FCC code in the production image to ensure that it cannot be accessed following provisioning
2. Establishing Trusted Connections to the Grid During Onboarding
Because OEMs often sit a step removed from the end customer, provisioning must remain flexible to accommodate their established workflows.
Some manufacturers create keys and certificates in‑house before bundling them into a factory configurator utility (FCU). The FCU operates alongside the manufacturer’s factory tool to configure and inject a device with the credentials, which in turn validates the smart meter’s operational parameters. While this method is efficient, both approaches deliver comparable security.
Since an OEM cannot foresee where a meter will ultimately be deployed or which utility account it will join, ensuring that the final grid connection is trustworthy is paramount. Manufacturers and utilities therefore employ pre‑shared keys (PSK) coupled with an enrollment list. This process verifies the unique ID, matching it to the credentials stored in a specific Device Management account; the device is then assigned to that account only if the ID matches the one uploaded in the utility provider’s IoT portal.
PSKs provide a common key that is securely provisioned into the device and represents the most basic level of security. However, because the credential is pre‑distributed, there is a risk that the list could be compromised, exposing millions of meters and their data. A public key infrastructure (PKI) offers a stronger alternative. By using PKI, the introduction between a device and the IoT platform is authenticated with asymmetric cryptography, tying the cryptographic signature to the third party that validates the meter. This ensures that credentials are generated solely on the device and never stored elsewhere.
While offering flexibility for OEMs, any reputable IoT partner will maintain security by guaranteeing a unique identity during the bootstrap stage. The interaction occurs as part of the data transfer with the Bootstrap Server over encrypted TLS communications, designed to thwart eavesdropping, tampering or message forgery.
Internet of Things Technology
- Smart Manufacturing Meets Big Data: Unlocking Predictive Efficiency and Innovation
- Smart Data: Navigating the Next Frontier of IoT and Big Data
- Outsourcing AI and Deep Learning in Healthcare: Protecting Data Privacy
- Can Security and Privacy Hinder the IoT Revolution?
- How Interconnectivity Drives Efficiency, Safety, and Sustainability in Modern Workplaces
- Navigating Security Challenges in Next‑Generation 5G and IPv6 Networks
- Securing the 20th Anniversary of the Internet of Things: Protecting Our Hyperconnected Future
- Industrial IoT & Smart Pneumatics: Accelerating Predictive Maintenance in Manufacturing
- Privacy Trends to Shape the Next Decade of IoT
- 5G: Preparing for Exponential Data Growth in Telecom



