Aligning IoT Security Strategies with Operator Ambitions in the Growing IoT Market
Operator’s Role in the IoT Value Chain
We forecast that 6.4 billion IoT connections worldwide will use fixed, mobile and low‑power wide‑area (LPWA) networks by 2025. As the IoT market expands, so does the security risk, making robust protection a central focus for all stakeholders.
An end‑to‑end IoT project spans diverse devices, platforms, layers and interfaces, creating multiple security touchpoints. Consequently, security has risen to the top of the priority list for IoT initiatives.
Telecom operators, acting as IoT service providers, must develop security capabilities that align with their overall strategy and ambition, according to Sherrie Huang and Michele Mackenzie of Analysys Mason.
Telecom Operators Need to Develop Security Offerings That Match Their IoT Proposition
Operators have long secured the connectivity layer with carrier‑grade, embedded security solutions. Secure transmission, data integrity, and user authentication have been embedded in operator networks for decades, and cellular networks are widely regarded as secure and reliable.
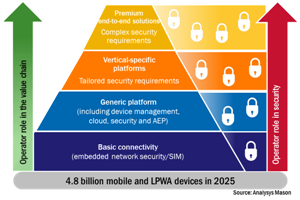
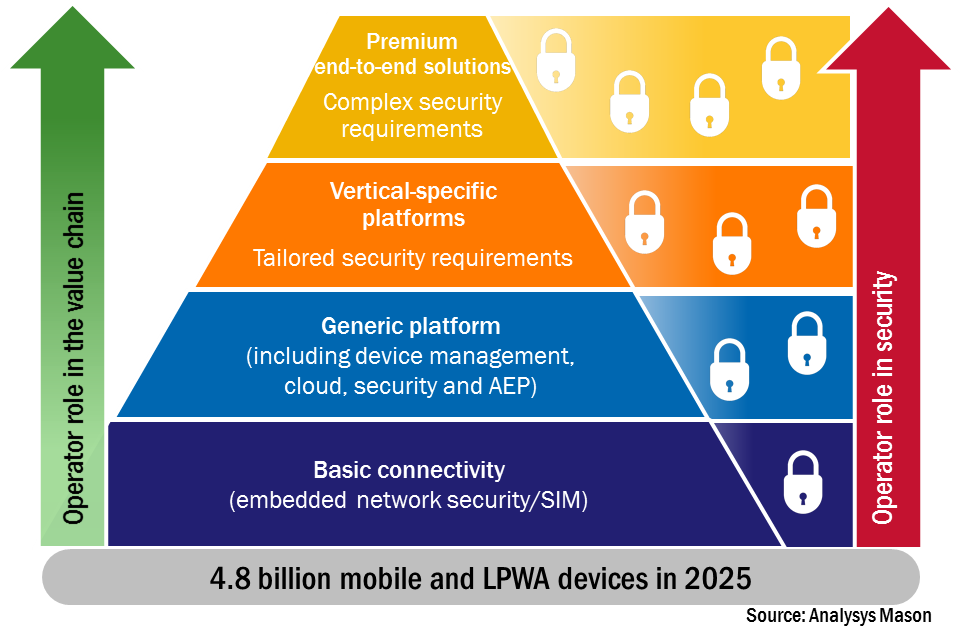
In the IoT market, operators are increasingly addressing components beyond connectivity to capture larger revenue shares. Advancing up the value chain requires specialist security expertise that many CSPs currently lack.
Operators will need to:
- Map their security offerings closely to the IoT components of the value chain they provide—application, device, and enabling capabilities such as hosting—recognizing that device security beyond SIM authentication may be new territory.
- Tailor security solutions for target verticals, incorporating technical requirements, regulatory compliance (e.g., GDPR in the EU), and business models.

Operators will need to partner or invest to align their security offering with their IoT proposition. Those with an internal cybersecurity unit, such as Telefónica and Vodafone, may already possess the necessary skills to build solutions in‑house, but most will still benefit from external partnerships or acquisitions.
Strategic investments or acquisitions can signal a firm’s intent and strengthen its position in the value chain. This bold approach is not limited to global operators—regional players like KPN and Tele2 have also acquired firms to bolster their security credentials.
Although security is unlikely to generate a significant standalone revenue stream, it is crucial for winning new business and differentiating an operator’s service from competitors.
Security Can Help Operators Differentiate and Strengthen Their LPWA Service
By 2025, more than half of all wide‑area IoT connections will be on LPWA networks, presenting unique challenges. Many LPWA devices are low‑power with limited computing resources, restricting available security options.
Operators deploying 3GPP standards (NB‑IoT and LTE‑M) have a prime opportunity to differentiate early in the LPWA market by highlighting the inherent secure nature of their networks. Despite the clear benefits, operators have been slow to market the value of embedded, standardised security.

Integrating additional security layers from the outset may increase upfront costs but ultimately reduces lifecycle costs by simplifying device updates and maintenance.
Operators could position security as a core differentiator by:
- Promoting the embedded security attributes of their network—such as SIM‑based authentication—and marketing their connectivity and device‑management platforms’ capabilities for anomaly detection, quarantine, and OTA updates.
- Developing new, cost‑effective security layers—often through partnerships—tailored to LPWA solutions, such as advanced SIM‑based protection.
- Ensuring that their security offering covers every component of the value chain, leveraging professional services and in‑house cybersecurity teams to advise and implement solutions.
IoT Security Could Be an Important Differentiator
While IoT security solutions may not generate substantial direct revenue, embedded security at the connectivity layer adds undeniable value. Additional security layers for other value‑chain components are premium services that are unlikely to drive large revenue streams but are essential for winning IoT business and setting operators apart from the competition.
The authors of this blog are Sherrie Huang, senior analyst, and Michele Mackenzie, principal analyst at Analysys Mason.
Internet of Things Technology
- Securing the Industrial IoT: A Practical Roadmap
- Two Essential Strategies for IoT Security
- Leveraging IoT for Early Wildfire Detection and Prevention
- Connecting the Remote World: How Satellite IoT Expands Global Coverage
- Designing Security into the Industrial IoT: Expert Guidelines for Protecting IIoT Systems
- AIoT: Harnessing the Synergy of Artificial Intelligence and the Internet of Things
- Securing Your IoT Ecosystem: Expert Strategies to Counter Ransomware and Cyber Threats
- Bridging the Skills Gap in the IoT Market: Challenges and Solutions
- IoT Revolutionizing Field Service: Predictive Maintenance & Higher ROI
- Three Key Questions Network Operators Must Ask to Secure IoT Deployments



