Unconfigured IoT Devices: The Hidden Threat to Your Smart Home

The proliferation of connected appliances has transformed everyday objects into “smart” devices. While this connectivity offers convenience, it also introduces significant security gaps, according to Ken Munro, partner at Pen Test Partners.
Many consumers purchase IoT products and leave them in their default state, effectively treating them as open, unencrypted Wi‑Fi access points. This practice creates a vulnerable entry point that attackers can exploit without any specialized knowledge.
Despite industry advisories, the specific risk of unconfigured devices remains largely unaddressed in both manufacturer guidance and regulatory frameworks, including the Code of Practice for Consumer IoT Security.
Attack Vectors
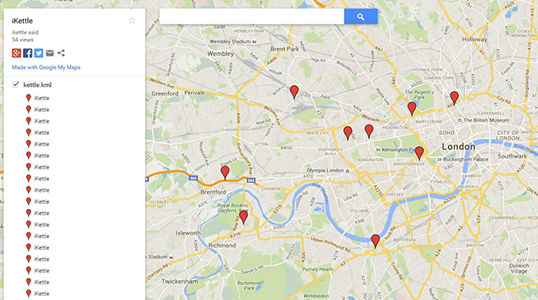
Identifying an unconfigured device is straightforward. An attacker can locate the SSID via geolocation services such as wigle.net. Common examples include:
- Kettles – SSID:
iketttle - Hot tubs – SSID:
BWGSPa - Google Chromecast – SSID:
Chromecast - LG air conditioners – SSID:
LGE_AC - EcoWater smart water softeners – SSID:
H2O-6c
Once the SSID is known, the attacker simply downloads the corresponding app, connects to the access point, and gains control.
Bluetooth‑enabled devices pose an even greater risk. Many lack authentication mechanisms, allowing any nearby device to pair freely. This blind acceptance can provide attackers with a backdoor into the home or corporate network.
We have observed such a scenario in an enterprise setting, where an unconfigured screencaster installed by an AV engineer bridged the wired and wireless corporate network, bypassing security controls.
Unconfigured devices often remain in warehouses until shipped, meaning they arrive with outdated firmware. Once connected to a network, they become prime targets for rogue firmware deployments that can enable eavesdropping or other malicious activities.
Long‑term devices—smart bulbs, thermostats, etc.—are especially problematic because users frequently neglect updates, leaving them exposed for extended periods.

Solutions
Design changes can mitigate this risk. A simple physical button that must be pressed to initiate wireless or Bluetooth pairing would force users to consciously authorize each connection, dramatically reducing accidental exposure.
Another cost‑effective approach is to ship all IoT devices with their radio modules disabled by default. Users can then enable connectivity only when they are prepared to manage the associated security responsibilities.
Ultimately, ownership of technology must rest with the consumer, not the manufacturer. By granting users the choice to keep devices offline, we can prevent our smart homes from becoming local Wi‑Fi attack surfaces.
The author is Ken Munro, partner, Pen Test Partners.
Internet of Things Technology
- Eclipse Vorto: Empowering Seamless IoT Device Integration
- How 5G Fuels IoT: Current State, Opportunities, and Key Challenges
- Why Wi‑Fi‑Enabled IoT Devices Pose a Growing Security Threat
- Effective Lifecycle Management for Industrial IoT Deployments: Monitoring, Service, Update, and Decommissioning
- IoT Security: Unpacking the Unique Threat Landscape for Connected Devices (Part 1)
- Securing the IoT: Proactive Strategies to Beat Emerging Threats
- Enterprise IoT Adoption Surges — Why Security Risks Are Growing
- Securing the $6 Trillion Future: Why IoT Standards and Regulation Matter
- Mitigating the Cyber Risks of IoT: Strategies and Insurance Solutions
- The Rising Threat of Kill‑Chain Attacks on IoT Devices – What Businesses Must Know



