Enterprise IoT Adoption Surges — Why Security Risks Are Growing

Deepen Desai of Zscaler explains how the rapid expansion of IoT in enterprises is creating new cyber‑attack vectors.
Globally, companies are integrating IoT devices to boost efficiency, streamline communication, and gain real‑time insights into system performance. According to Gartner, 20.4 billion IoT devices will be in use worldwide by 2020, and more than 65% of enterprises are expected to adopt them.
However, the swift rollout of these devices has outpaced the security controls that protect them. Many IoT gadgets are employee‑owned and use weak, factory‑default passwords, making them attractive targets for cybercriminals. As Zscaler notes, IoT technology often advances faster than the safeguards that keep it secure.
Researchers have already demonstrated remote hacks on pacemakers and vehicles. A landmark incident occurred in October 2016 when the Mirai botnet launched a massive DDoS attack against DNS servers on the U.S. east coast, disrupting services worldwide. The attack traced back to IoT devices—wireless routers and connected cameras—that were compromised.
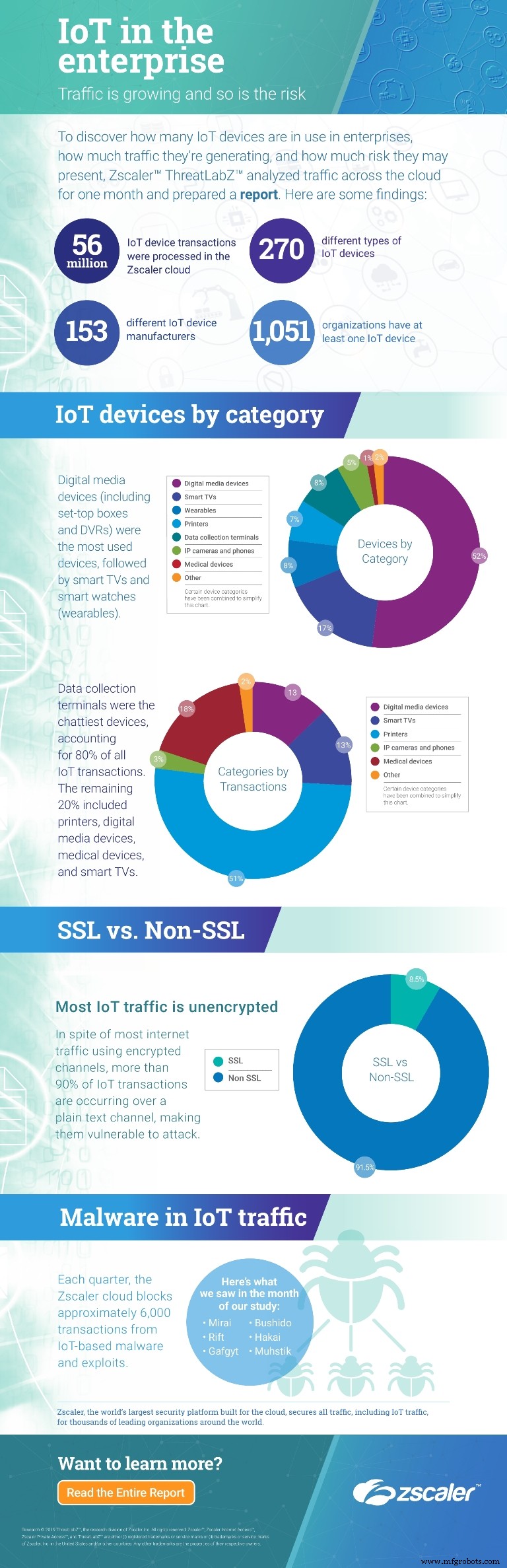
In our recent study, “IoT in the Enterprise: an Analysis of Traffic and Threats,” we found that most IoT traffic travels over plain‑text channels rather than secure SSL/TLS, exposing sensitive data. This is just one of many vulnerabilities: many devices ship with pre‑set passwords that are rarely changed.
Like any internet‑connected device, IoT units are susceptible to malware. Yet, most IoT hardware on the market today lacks built‑in security and offers no straightforward patching mechanism. Many organizations mistakenly believe that because IoT devices do not store data, they pose minimal risk—an assumption that the Mirai attack disproved.
Enterprises can mitigate these risks by implementing several best practices:
- Change default credentials to strong, unique passwords.
- Encourage employees to keep firmware updated and to use robust authentication.
- Place IoT devices on isolated, segmented networks to limit lateral movement.
- Restrict inbound and outbound traffic, blocking unnecessary ports from external access.
- Apply regular security and firmware updates.
- Maintain visibility into “shadow” IoT devices that may already be present on the network.
With the proliferation of connected devices and the flood of data they generate, legacy networks will struggle to provide adequate protection. The threat landscape has evolved, and enterprises must act swiftly to secure their IoT deployments.
Author: Deepen Desai of Zscaler.
Internet of Things Technology
- How 5G Fuels IoT: Current State, Opportunities, and Key Challenges
- Building the Foundation for Enterprise IoT Success
- Unconfigured IoT Devices: The Hidden Threat to Your Smart Home
- How IoT and Cloud Computing Shape the Future of Enterprise Data
- Securing the $6 Trillion Future: Why IoT Standards and Regulation Matter
- Mitigating the Cyber Risks of IoT: Strategies and Insurance Solutions
- AIoT: How Artificial Intelligence Amplifies the Internet of Things
- Top 6 IoT Trends Shaping 2016 and Beyond
- Key Drivers for Successful Enterprise IoT Development: Insights from Nokia Experts
- The Rising Threat of Kill‑Chain Attacks on IoT Devices – What Businesses Must Know



