How RISC‑V Is Strengthening Security for IoT‑Connected Devices
RISC‑V hardware delivers robust security for IoT‑connected embedded devices, surpassing what software alone can achieve.
As the Internet of Things expands, protecting embedded devices demands a shift from software‑centric cybersecurity to hardware‑based safeguards. RISC‑V provides that next‑level defense.
Once considered a futuristic concept, the IoT is now a tangible reality. Analysts forecast that the number of connected devices could exceed 75 billion by 2025.
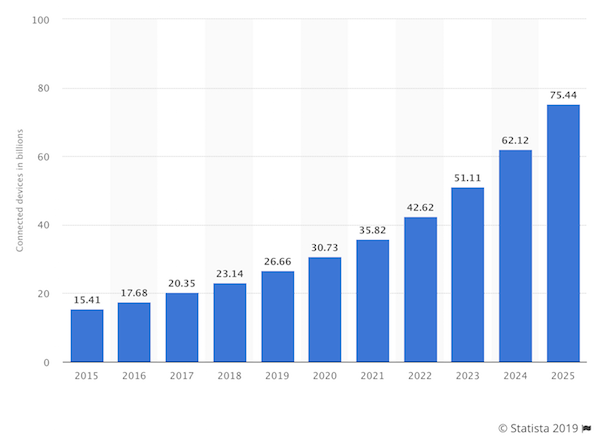
Figure 1. Projected growth of IoT‑connected devices from 2015 to 2025. Image courtesy of Statista.
While the term IoT often evokes smart appliances, the majority of deployments are corporate. A 2018 Trustwave survey revealed that 64 % of surveyed organizations had already introduced IoT devices, with an additional 20 % planning deployment in 2019.
Despite the rapid adoption, only 28 % of respondents view an IoT cybersecurity strategy as “very important.” This gap underscores a pressing disconnect: consumers and businesses demand more devices, yet few prioritize security.
Device manufacturers, however, recognize the vulnerability risk. An Eclipse Foundation report identified security requirements as the top obstacle for 60 % of respondents when developing connected products.
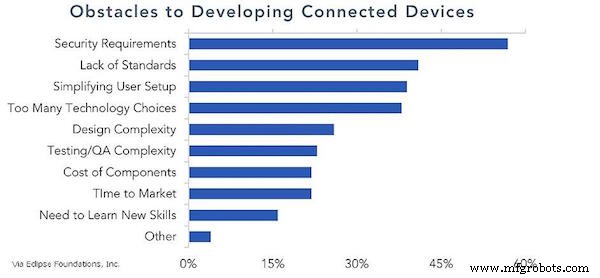
Figure 2. Primary barriers to developing connected devices, according to makers. Image courtesy of Eclipse Foundation.
This misalignment threatens the industry’s growth. Corporations and consumers demand devices at scale, but device makers must balance rapid market entry with robust security.
RISC‑V offers a solution. While software defenses can mitigate some risks, hardware security is essential for the IoT’s long‑term success.
RISC‑V’s Opportunity to Secure the IoT
According to the Associated Press, cybercrime could cost companies $5.2 trillion over the next five years—driven by businesses’ heavy reliance on complex, internet‑enabled models that outpace adequate safeguards.
IoT expands attack surfaces, exposing critical assets to costly breaches. Software security alone is insufficient; on average, every 1,000 lines of code contain about 15 bugs, and roughly 2 % of those can be exploited, as noted by the FBI. Complex security software is itself a high‑risk component, riddled with vulnerabilities.
Effectively addressing this challenge requires embedding security directly into system‑on‑chip (SoC) designs. RISC‑V, an open‑source instruction set architecture (ISA) free of licensing fees, enables manufacturers to allocate resources toward hardware security rather than costly alternatives.
With lower cost and the flexibility of an open ecosystem, RISC‑V empowers the creation of next‑generation secure processors. If the RISC‑V Community can position itself as the benchmark for secure processing, it could become the ISA of choice for the projected $470 billion IoT market.
Dover’s RISC‑V‑Compatible CoreGuard® technology halts network‑based attacks, delivering genuine security, safety, and privacy for IoT deployments.
Industry Articles are a form of content that allows industry partners to share useful news, messages, and technology with All About Circuits readers in a way editorial content is not well suited to. All Industry Articles are subject to strict editorial guidelines with the intention of offering readers useful news, technical expertise, or stories. The viewpoints and opinions expressed in Industry Articles are those of the partner and not necessarily those of All About Circuits or its writers.
Internet of Things Technology
- IoT Cybersecurity: 5 Essential Steps to Safeguard Your Applications
- Edge AI Gains Momentum: Cloud Leaders AWS and Microsoft Show Integrated Inference & Management Solutions
- How the IoT Cybersecurity Improvement Act Shapes the Future of Connected Devices – What Businesses Need to Know
- Safeguarding IoT Adoption: Proven Cybersecurity and Privacy Strategies for Enterprises
- The IoT Surge: Why Strong Cybersecurity Is Critical for Connected Devices
- Why a Global Standard for Consumer IoT Security Is Essential
- How IoT Revolutionized Healthcare During the Covid‑19 Pandemic
- Protecting IoMT: Best Practices for Securing Internet-Connected Medical Devices
- Protecting Flash Memory in IoT & Edge Devices: Best Practices & Security Trends
- IoT Devices Set to Outpace Non-Connected Tech, Reaching 30B by 2029



