Securing Your IoT Product: A Practical Guide to Preventing Hacker Attacks
IoT security is complex and high‑stakes. A breach can put human lives at risk when hackers hijack real‑world objects, and the physical device itself becomes a new attack vector. How can you shield your product across every layer of the stack?

Picture this: you’re sipping your Sunday coffee when the news reports that a connected device was hijacked. The story focuses on the very product you built, and you realize a hidden flaw was exploited. The reality is that the “it won’t happen to me” mindset can be dangerously misleading.
Before IoT, attackers mainly targeted data—identity theft, credit‑card fraud, or denial‑of‑service. Today, with IoT, a cyber attack can directly manipulate physical systems and potentially cause injury or death.
- Elevator stuck with all passengers trapped
- Self‑driving car taken over mid‑drive
- Aircraft turbine controller forced to malfunction
- Factory robotic arm moves unpredictably
- Smart‑home locks opened by intruders
- Hospital equipment compromised, endangering patients
An IoT security breach can put human lives at risk.
Security must be woven into the DNA of your product, not added after the fact. As a Product Manager who may not be a security expert, the key is to evaluate risk at each layer of the IoT stack and create an actionable roadmap.
Evaluate Security at Every Layer of the IoT Stack
Security is broad, but breaking it down by stack layer makes it manageable. By assessing risk across the physical device, embedded software, communications, cloud platform, and applications, you can target the most critical threats first.
Related post: Take Control of Your IoT Strategy with the IoT Decision Framework.
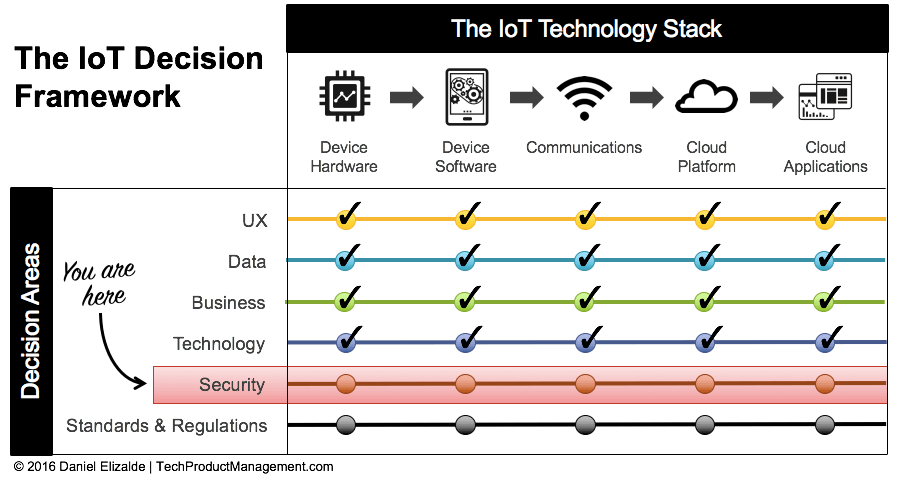
Two core vectors require focus:
- Physical tampering at the device level
- Cybersecurity across embedded software, communications, cloud, and applications
1. Protect Against Physical Tampering
With millions of devices deployed in close proximity, physical access becomes a lucrative attack surface. Consider a hospital that invested heavily in network security only to discover a Trojan infiltrated through a USB port used by a nurse’s Android phone.

Physical tampering can occur through exposed ports, power interruption, theft, or component removal. Conduct a threat model for your device:
- What damage could a malicious actor cause with physical access?
- Could they establish a backdoor into your network or customers’ systems?
- What safeguards can you enforce—locked enclosures, tamper‑evident seals, or remote disabling?
Concrete mitigations:
- Eliminate or secure all physical connectors
- Use access control mechanisms (keypads, biometrics, or RFID)
- Design for installation in protected locations (locked rooms, high ceilings)
2. Protect Against Cybersecurity Attacks
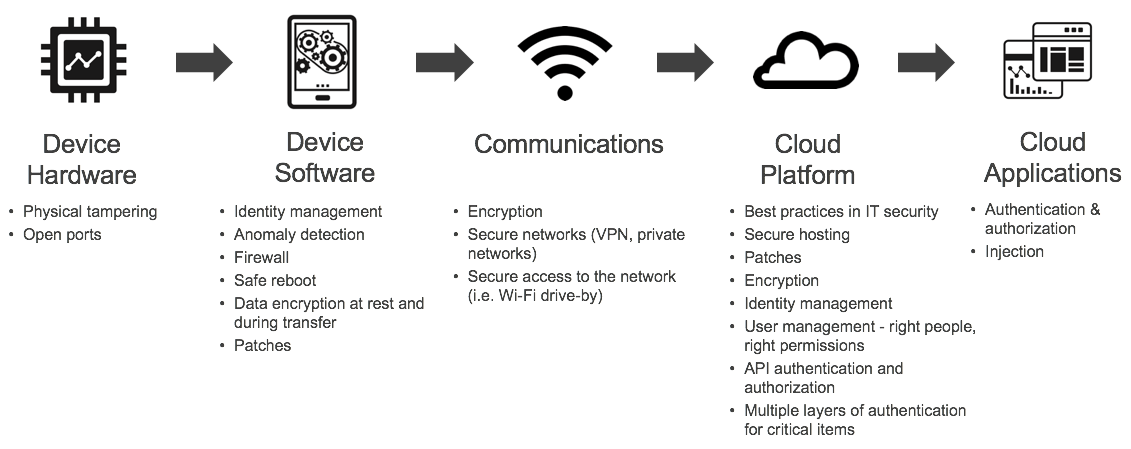
Traditional cybersecurity principles—encryption, secure authentication, role‑based access control—apply across all non‑physical layers. Because these layers are often developed by separate teams, the Product Manager’s role is to enforce consistency and coordinate risk assessments.
Walk through the IoT Technology Stack with your engineering leads, identify vulnerabilities at each layer, and map out mitigations. A typical plan might look like this:
The Bottom Line
Your mandate as a Product Manager is not to become a security guru but to embed security at every layer of the stack. Use the IoT Decision Framework to surface gaps and craft a defensive strategy that evolves over time.
Remember, security is a continuous journey. New exploits surface daily, so maintain a proactive posture—regularly update firmware, monitor threat intelligence, and audit third‑party components.
Upcoming posts will cover internal threat mitigation—how to safeguard your product from vulnerabilities introduced within your own organization. Subscribe to stay informed (your email is never shared, and you can unsubscribe at any time).
If you found this guide helpful, please share it with your network!
Internet of Things Technology
- Protecting Aluminum Against Corrosion: Expert Strategies for Long‑Lasting Durability
- Creating a Stakeholder‑Focused IoT Product Roadmap
- Turning IoT Data into Actionable Insights: A Proven Data Strategy Framework
- Smart Security: Expert Strategies to Shield Your Home IoT Devices from Hackers
- IoT Risks: Protecting Your Business from Smart‑Device Vulnerabilities
- Protect Your Business: Expert Cybersecurity Strategies for Manufacturers
- Safeguarding Industrial Electronics from Lightning Damage: Proven Protection Strategies
- Powering Your IoT Projects to Success
- Shield Your Business from Phishing Attacks: Proven Strategies & Expert Tips
- From Concept to Production: Navigating Design to Fabrication



