Intrusion Detection Systems: Protecting Your Network with Smart Alerts
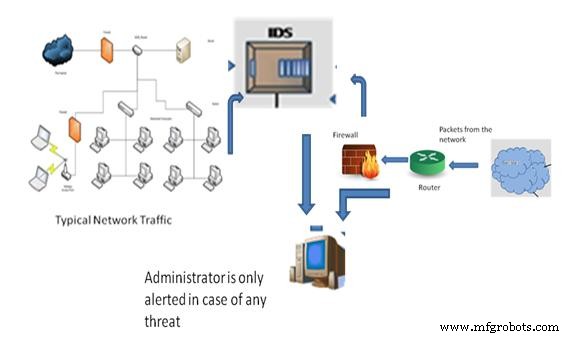
"Life was simpler before World War II. After that we had systems." — Admiral Grace Hopper. The rapid expansion of computer networks has made data sharing essential, but it also exposes critical assets to evolving cyber threats. Firewalls act as the first line of defense, filtering traffic, but they do not notify administrators when an attack is underway. That’s where an Intrusion Detection System (IDS) steps in.
An IDS functions like a burglar alarm for IT environments. It monitors activity, identifies malicious attempts, and alerts the administrator in real time, allowing a swift response before damage occurs.
Understanding Firewalls vs. IDS
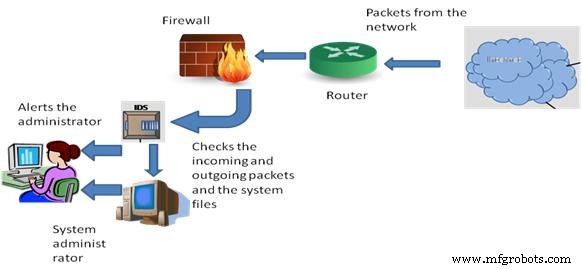
Firewalls—software or hardware—serve as gatekeepers, blocking known harmful packets. They can inspect only portions of a packet or the entire payload, but they cannot inform you when an intrusion has succeeded. IDS complements firewalls by providing continuous monitoring and situational awareness.
Classification of Intrusion Detection Systems
IDS can be categorized by the system they protect and by their detection methodology.
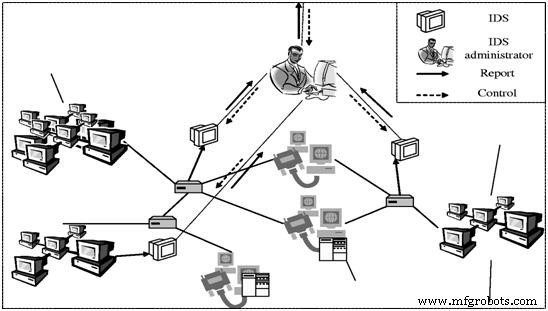
- Network IDS (NIDS): Deployed at network boundaries or between networks and servers, a NIDS scans traffic across subnets, comparing it to a database of known attack signatures. Its advantage is broad coverage without installing software on each host.
- Host IDS (HIDS): Installed on individual machines, a HIDS scrutinizes inbound/outbound packets and audits system files for unauthorized changes. It provides deep visibility into a single host without extra hardware.
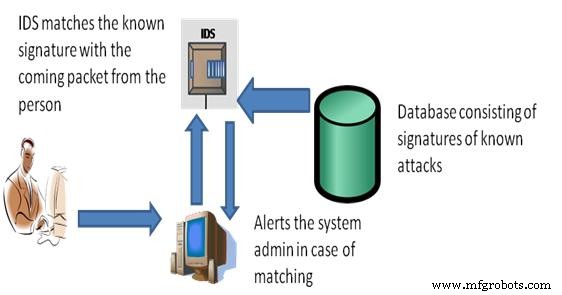
- Signature‑Based IDS: Relies on a database of known attack signatures. When a packet matches a signature, an alert is triggered. It offers high accuracy for known threats.
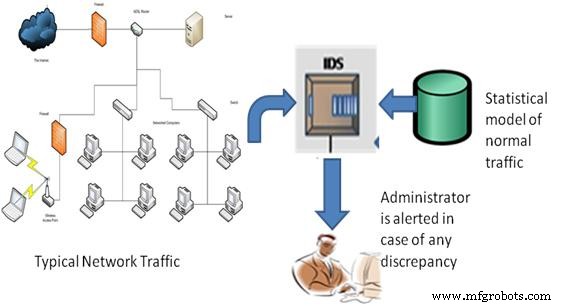
- Anomaly‑Based IDS: Builds a statistical model of normal network behavior—bandwidth, protocols, ports, and devices—and flags deviations. It excels at detecting zero‑day or novel attacks.
- Passive IDS: Detects malicious activity and issues alerts; the administrator then decides on remedial action.
- Reactive IDS (Intrusion Prevention System): In addition to detection, it actively blocks or resets suspicious connections, providing real‑time defense.
Key Features of a Robust IDS
- Continuous monitoring of user and system activity.
- File integrity and configuration auditing.
- Pattern analysis against known attack signatures.
- Detection of misconfigurations and security gaps.
- Real‑time alerts and detailed logging.
Free IDS Tools Worth Considering
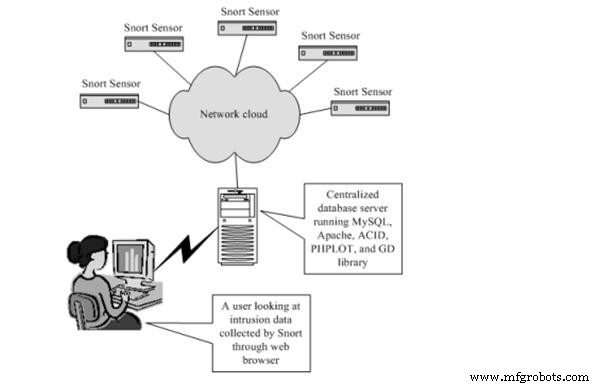
Snort
Snort is the industry‑standard open‑source IDS, widely adopted by enterprises and security professionals. It performs real‑time packet capture, protocol decoding, rule‑based detection, and alerting. According to the Snort project, it processes up to 1 Gbps on commodity hardware.
Snort Architecture
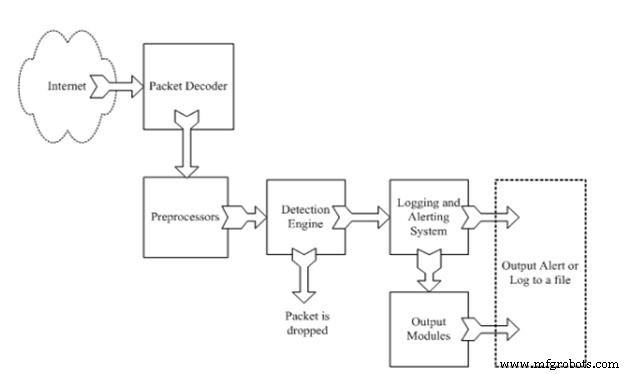
- Packet Decoder: Extracts packets from the network interface and prepares them for analysis.
- Preprocessor: Normalizes data, reassembles fragmented packets, and decodes TCP streams.
- Detection Engine: Applies user‑defined rules to each packet; matched packets trigger alerts or actions.
- Logging & Alerting: Captures detailed event logs and notifies administrators via email, syslog, or third‑party integrations.
- Output Modules: Customizable interfaces for exporting alerts to SIEMs or dashboards.
Why Deploy an IDS?
- Continuous visibility into network and host activity.
- Customizable to the specific threat landscape of an organization.
- Prevents or mitigates damage from both internal and external attacks.
- User‑friendly dashboards simplify incident response.
- Rapid detection of unauthorized file changes and policy violations.
While IDS can’t always pinpoint the origin of an attack, its real‑time alerts enable faster containment and recovery. For deeper insight or implementation guidance, feel free to share your questions in the comments below.
Sensor
- Master Java Input & Output: Print, Read, and Format Your Data
- Motion Detection Alarm System with Java & Reactive Blocks – Deploy on Raspberry Pi & Send SMS
- Training a Basic Perceptron Neural Network with Python: Step‑by‑Step Guide
- Strengthen Your Maintenance System Before Adding New Programs
- Transforming MEP: From Local Systems to a National Manufacturing Network
- 5 Essential Network Security Strategies for Small Businesses
- Advanced Arduino Collision Warning System – Visual & Audio Alerts for Vehicle Safety
- IoT-Powered Gas Detection System: Enhancing Safety in Hospitality and Industrial Settings
- Ultra‑Sensitive Chemical Weapon Detection System for Low‑Level Threats
- Automated Ultrasonic In‑Situ Monitoring for Composite Cure Defect Detection



