







Cloud Computing

Cloud monitoring tools help assess the state of cloud-based infrastructure. These tools track the performance, safety, and availability of crucial cloud apps and services. This article introduces you to the top 30 cloud monitoring tools on the market. Depending on your use case, some of these tools
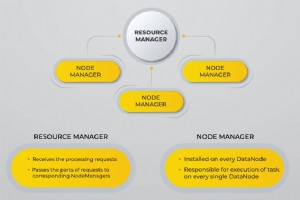
The evolution of big data has produced new challenges that needed new solutions. As never before in history, servers need to process, sort and store vast amounts of data in real-time. This challenge has led to the emergence of new platforms, such as Apache Hadoop, which can handle large datasets wi
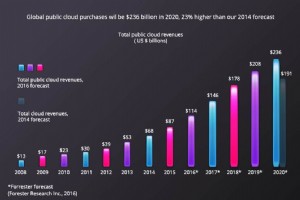
Much has changed since organizations valued on-premise infrastructure as the best option for their applications. Nowadays, most companies are moving towards off-premise possibilities such as cloud and colocation. Forrester Inc. reports that Global spending on Cloud services has exponentially increa
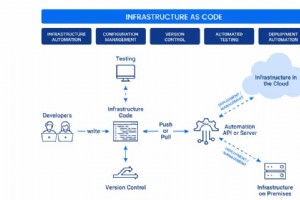
Infrastructure as Code (IaC) enables developers to provision IT environments with several lines of code. Unlike manual infrastructure setups that require hours or even days to configure, it takes minutes to deploy an IaC system. This article explains the concepts behind Infrastructure as Code. You
In today’s modern technology space, companies are opting to migrate from on-premises hardware to hosted solutions. Every business wants the optimal cohesion between the best technology available and a cost-effective solution. Identifying the unique hosting needs of the business is crucial. This dec
Do you assume that your data in the cloud is backed up and safe from threats? Not so fast. With a record number of cybersecurity attacks taking place in 2018, it is clear that all data is under threat. Everyone always thinks “It cannot happen to me.” The reality is, no network is 100% safe from hac

Hospitals, clinics, and other health organizations have had a bumpy road towards cloud adoption over the past few years. The implied security risks of using the public cloud or working with a third-party service provider considerably delayed cloud adoption in the healthcare industry. Even today, wh

In this article you will learn: Understand what a Security Operations Center is and active how detection and response prevent data breaches. Six pillars of modern security operations you can’t afford to overlook. The eight forward-thinking SOC best practices to keep an eye on the future of cybers

Modern data centers use physical servers with hypervisors to run virtual machines. This way, virtualization brought cost-effectiveness and enhanced scalability. With virtualized network solutions, such as VMwares NSX software, the concept of networking acquired a new meaning. The software-defined n
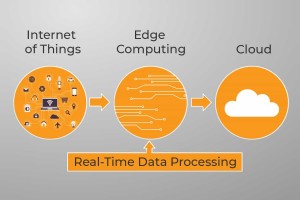
The term “Edge computing” refers to computing as a distributed paradigm. It brings data storage and computes power closer to the device or data source where it’s most needed. Information is not processed on the cloud filtered through distant data centers; instead, the cloud comes to you. This distr

As technology rapidly advances, there are numerous options available to businesses for running applications and software on the cloud. Several factors need to be considered when deciding if cloud infrastructure is the right choice. We’ll go through the main pros and cons of Cloud-based ERP (Enterpr
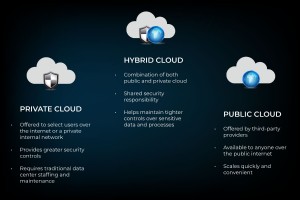
Cloud technology has opened up new possibilities for public, private, and hybrid clouds. Many organizations are migrating to the hybrid cloud to get the most out of cloud computing. A hybrid cloud provides flexibility and the freedom to balance their investing needs between on-premises cloud techno

After years of design stability, we will look into how businesses should adapt to an IT infrastructure that is continuously changing. Corporate-wide area networks (WANs) used to be so predictable. Users sat at their desks—servers at company data centers, stored information, and software application
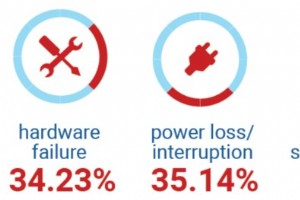
Your business data is under constant threat of attack or data loss. Malicious code, hackers, natural disasters, and even your employees can wipe out an entire server filled with critical files without anyone noticing until it is too late. Are you willing to fully accept all these risks? What is Clo

As your business grows, so does your need for secured professional data storage. Your digital database expands every day with each email you send and receive, each new customer you acquire, and each new project you complete. As your company adopts new business systems and applications, create mor

Nearly 30% of the entire internet runs on WordPress. WordPress performance issues are well known. The fact is, you have seconds, if not fractions of a second, to convince users to stay on a web page. When a webpage’s loading time increases from just 1 to 3 seconds, the probability of the user leavi

Choosing a cloud service provider is without question more involved than choosing the first result from a Google search. Each business has different requirements, customizations, and financial responsibilities. It is crucial for the perfect service to meet and exceed businesses expectations. That s

Your company is facing new cybersecurity threats daily. Learn how Security as a Service (SECaaS) efficiently protects your business. The cybersecurity threat landscape is rapidly expanding. Technology professionals are fending off attacks from all directions. The lack of security expertise in many

Cloud monitoring is a suite of tools and processes that reviews and monitors cloud computing resources for optimal workflow. Manual or automated monitoring and management techniques ensure the availability and performance of websites, servers, applications, and other cloud infrastructure. Continual

When adopting cloud technology, security is one of the most critical issues. Many Organizations still fear that their data is not secure in the cloud environment. Companies want to apply the same level of security to their cloud systems as their internal resources. It is essential to understand and
Cloud Computing