Community-Driven Hardware CWE: A New Framework for Identifying Design Security Weaknesses
Modern computer systems are more advanced—and more complex—than ever, and the sophistication of cyberattacks is escalating at a staggering pace. While the industry has long focused on hardening software, attackers are increasingly targeting the hardware layer, exploiting vulnerabilities that arise during design, manufacturing, and operation.
Academic and industry research has documented advanced hardware‑based attack techniques—often blending hardware and software exploits—demonstrating that public‑domain knowledge gives hackers a significant advantage. Hardware designers, however, lack a unified taxonomy and shared knowledge base comparable to the well‑established Common Weakness Enumeration (CWE) and Common Vulnerabilities and Exposures (CVE) systems for software.
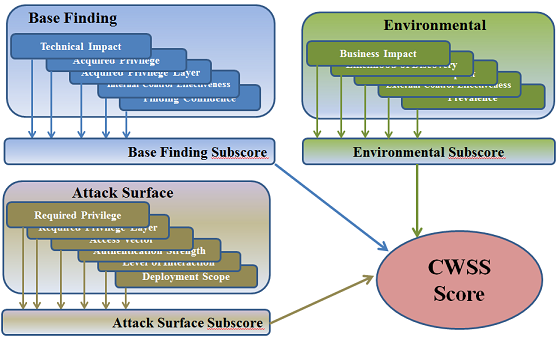
Common Weakness Scoring System (CWSS) (Source: Mitre)
Software architects and developers rely on the Mitre‑developed CWE and CVE databases to identify and avoid security flaws in code. These resources enable a collective effort to detect, catalog, and remediate vulnerabilities across the software ecosystem.
As hardware becomes a primary target, the industry must establish an equally comprehensive repository for hardware design weaknesses. Such a framework would empower practitioners to address key questions:
- Where are the critical hardware entry points in my design?
- Which design weaknesses should I monitor most closely?
- How do temperature, voltage, or current excursions affect device properties, and how might attackers exploit these anomalies?
- What are the potential impacts of a successful hardware attack on the device, the software stack, and the overall system?
- What recent incidents illustrate these vulnerabilities?
- How can validation teams detect and mitigate flaws early in the product life cycle?
- What mitigation strategies exist, and what are their cost‑effectiveness trade‑offs?
To meet this need, a standardized, openly accessible language for hardware security is essential—one that enables researchers, vendors, and designers to share findings and best practices efficiently.
In a significant milestone, Intel and Mitre partnered last summer to launch the first version of a hardware‑centric CWE. In February 2020, Mitre released CWE 4.0, expanding its focus beyond software to include hardware design vulnerabilities. The goal is to help designers recognize potential pitfalls in specific IP blocks and to educate future professionals on common hardware mistakes.
The new CWE Hardware Design View already lists 30 hardware issues that are frequently overlooked. These are organized into high‑level categories such as Manufacturing and Lifecycle Management, Security Flow, Privilege Separation, General Circuit and Logic, Core and Compute, Memory and Storage, and Cryptographic Primitives, among others.
Although this represents a crucial first step, the collection will grow as the community contributes new entries and examples. Industry, academia, and government stakeholders must collaborate to expand and refine this cumulative hardware CWE.
A robust hardware CWE will allow architects to implement proven mitigations, keep designers updated on secure‑by‑design practices, and enable verification engineers to detect vulnerabilities throughout development. Researchers can more readily pinpoint systemic hardware risks, devise effective fixes, and collaborate across disciplines. Ultimately, a comprehensive, open hardware CWE accelerates the evolution of secure hardware for the devices we depend on daily.
For too long, classifying hardware weaknesses has seemed daunting. As hardware remains a prime attack vector, the urgency to catalogue and evaluate these vulnerabilities—on par with software threats—has never been greater. CWE 4.0 offers a solid foundation for the industry to rally around, fostering a shared language and a safer hardware ecosystem.
>> This article was originally published on our sister site, EE Times.
Embedded
- Avoid Costly Surprises in Connected Hardware Design: Proven Strategies
- VE-VIDES Initiative Unveils Trustworthy Design & Verification Framework for IoT Security
- Mouser Stocks Infineon’s OPTIGA Trust X – Turnkey Hardware Security for IoT, Smart Homes, and More
- Lattice’s MachXO3D FPGA Strengthens Hardware Security with Root‑of‑Trust Features
- Hardware Security Leads IIoT with Tamper‑Resistance, Faster Market Entry, and Strong Protection for Manufacturing, Transport, and Utilities
- FPGA Hardware Resources for High‑Performance Embedded Systems
- Essential Hardware Security Vulnerabilities Every Engineer Must Understand
- SimpliSafe Security System Hack Exposes IoT Vulnerability: $2 Wireless Emitter Hacks Door Sensors
- Common PCB Design Challenges and How to Avoid Them
- How Robot Simulation Solves Design Challenges



