Silicon Labs Launches Secure Vault: A Hardware‑Based Solution to Strengthen IoT Device Security
When it comes to Internet of Things (IoT) security, chip vendors often hear the same criticism: designers and manufacturers do not treat security as a core requirement. The prevailing justification is that security adds cost, and if it isn’t essential, why bother? Many devices also incorporate security only as an after‑thought, leaving them vulnerable to compromise.
Across the globe, governments are tightening the rules. California’s SB‑327 took effect in January 2020, Europe’s ETSI standard now mandates cyber‑security for consumer IoT, and the UK government is drafting a new law on IoT security. In response, vendors are stepping up their awareness campaigns.
This week Silicon Labs announced a new hardware‑based security offering for its wireless system‑on‑chip (SoC) solutions. The Secure Vault technology is a comprehensive suite designed to help device makers tackle rising IoT threats and meet regulatory demands. It is already integrated into the Wireless Gecko Series 2 platform, which pairs software security features with physically unclonable function (PUF) hardware to reduce the risk of breaches and protect intellectual property.
Silicon Labs describes Secure Vault as a cost‑effective, wireless SoC that delivers an optimized security level. The subsystem—comprising a dedicated core, bus, and memory—is isolated from the host processor, ensuring that key management, cryptography, and other critical functions remain protected. This hardware separation is especially valuable for companies navigating GDPR in Europe and California’s SB‑327.
We asked Gregory Guez, Senior Director of Product Marketing for IoT Security at Silicon Labs, how Secure Vault differs from other solutions such as trusted execution environments (TEE). He explained, “Secure Vault provides isolation between the secure element and the customer application in hardware, not software. While other vendors may offer key management with limited storage, our PUF‑based design delivers secure key storage across the entire memory space.”
Secure Vault also offers tamper‑resistant encrypted keys. Guez added, “The encrypted keys are protected by configurable detectors and responses. Secure Vault’s secure identity certificates enable manufacturers to prove device authenticity—an essential requirement in today’s IoT ecosystem.”
Senior cybersecurity analyst Tanner Johnson of Omdia notes that embedded security is a non‑negotiable requirement. “Software updates alone can’t fix vulnerabilities rooted in insecure hardware. Hardware components must serve as the front line of defense, especially as new legislation targets IoT product security,” he said.
By combining hardware and software, Secure Vault helps manufacturers safeguard brand reputation, design integrity, and consumer data. Embedding the security system within the wireless SoC simplifies development and enables secure over‑the‑air (OTA) updates throughout the product lifecycle. Delivering genuine, trusted firmware mitigates unforeseen exploits, threats, and regulatory gaps.
Secure Vault addresses the four pillars of IoT security—confidentiality, authentication, integrity, and privacy—through secure device identity, robust key management, and advanced tamper detection.
Secure device identity solves the challenge of post‑deployment authentication. Silicon Labs’ factory‑based trust provisioning service generates a unique device‑identity certificate during IC manufacturing—akin to a birth certificate—allowing for post‑deployment security, authenticity, and attestation‑based health checks. The certificate guarantees the chip’s authenticity for its lifetime.
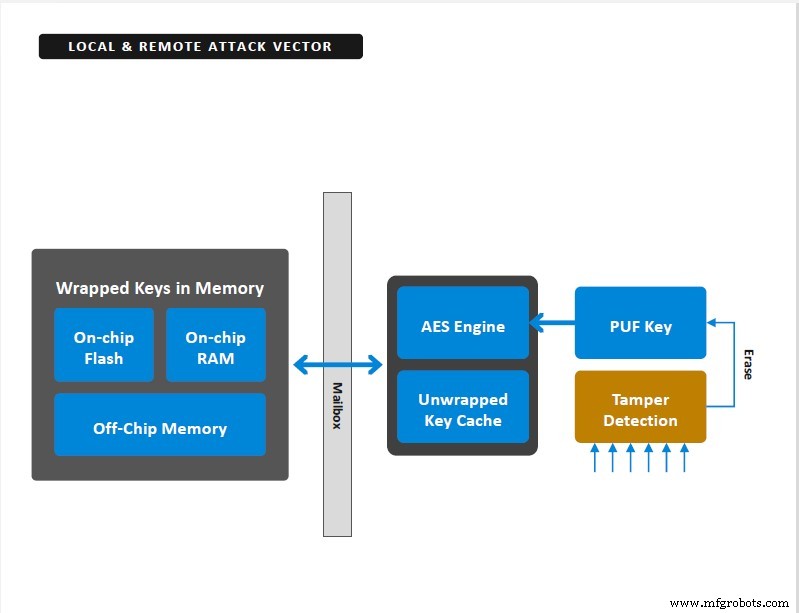
Secure Vault provides secure key storage, with keys encrypted using a master encryption key generated via a PUF (Image: Silicon Labs)
Key secrecy is critical for device and data access. Secure Vault encrypts and isolates keys from application code. All keys are encrypted with a master key generated by a PUF, and power‑up signatures are unique to each device. Master keys are created during power‑up, eliminating stored master keys and reducing attack vectors.
Tamper detection ranges from enclosure tamper resistance to sophisticated silicon‑level detection of voltage, frequency, and temperature manipulations. Configurable tamper‑response features let developers trigger interrupts, resets, or even secret key deletion when anomalies are detected.
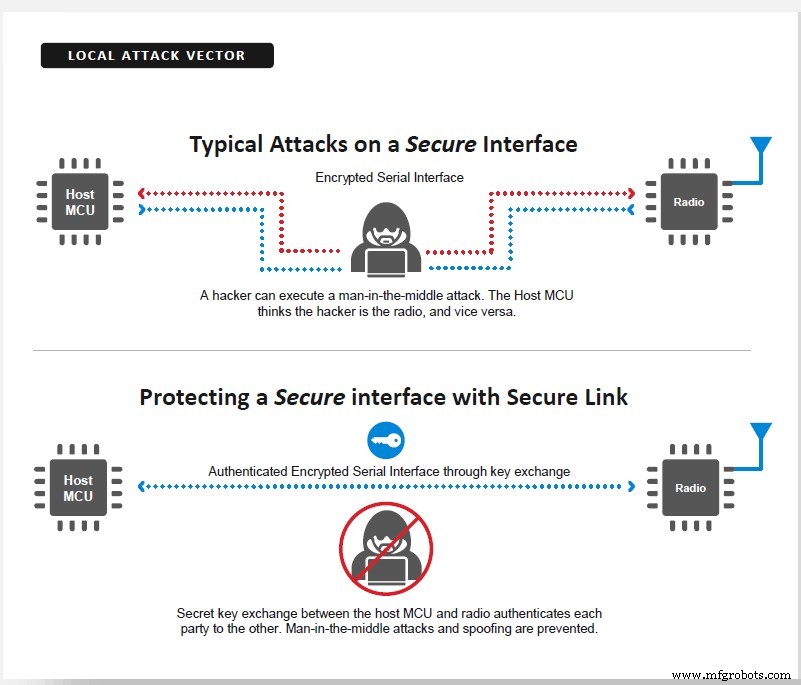
Secure Link encrypts the interface between a microcontroller and a Wi‑Fi chip to prevent attackers from gleaning SSIDs or passkeys (Image: Silicon Labs)
Additional Secure Vault features include anti‑rollback protection—preventing older, vulnerable firmware from being re‑loaded—and Secure Link, which encrypts the microcontroller‑Wi‑Fi interface using per‑session, per‑device Diffie‑Hellman key exchanges. The link is uniquely secured per device and keys are regenerated on every power cycle, making exploitation difficult.
Silicon Labs is currently sampling Secure Vault‑enabled wireless SoCs, slated for release in late Q2 2020.
Embedded
- How IoT Is Mitigating Security Risks in the Oil & Gas Industry
- Secure IoT: Best Practices for Building Trustworthy Connected Products
- Two Essential Strategies for IoT Security
- IoT Security – A Practical Guide from Perry Lea
- STMicroelectronics’ STSafe‑A100 Evaluation Kit: Accelerate Secure IoT Development
- Cypress Enhances IoT Security with PSA‑Certified PSoC 64 MCUs
- IoT Security – Who Holds the Responsibility?
- Building a Managed IoT Ecosystem That Works: Flexibility, Security & Standardization
- IoT Security Lessons from Recent Breaches: Protecting Your Enterprise
- Strengthening Industrial IoT Security: Proven Strategies & Best Practices



