Secure IoT: Best Practices for Building Trustworthy Connected Products
In the emerging vision of a hyper‑connected world, everyday objects are evolving into intelligent, responsive partners that can anticipate our needs.
Cyber‑Physical Systems Are Becoming the New Norm
Just a few years ago, the idea of pervasive computing felt like science fiction. Today, manufacturing lines that detect failures in real time, irrigation systems that adapt watering schedules to soil moisture, and office coffee machines that schedule maintenance autonomously are already mainstream, supported by proven business models. Companies worldwide are preparing for a future where cyber‑physical systems are ubiquitous.
“Our strategic target is for all our electronic product categories to be IoT‑enabled by 2020.”
– Volkmar Denner, Chairman, Robert Bosch GmbH
Security and Privacy Are the Pillars of IoT Success
Connecting devices is only the first step; enabling them to play an active role in business and daily life demands robust security and privacy. Without user confidence, data sharing and reliance on connected products will stall. Recent high‑profile IoT breaches underscore that the promise of “connected everything” is matched by the challenge of safeguarding billions of devices that were not originally designed for secure internet connectivity.
Trust is the enabler for societal acceptance of IoT innovations. Without confidence in security, reliability, and safety, widespread adoption—and the associated market opportunities—will remain unrealized.
Adopting a Holistic Security Approach
Securing IoT solutions requires a comprehensive strategy that spans the entire product lifecycle, covering processes, organizational governance, and technology.
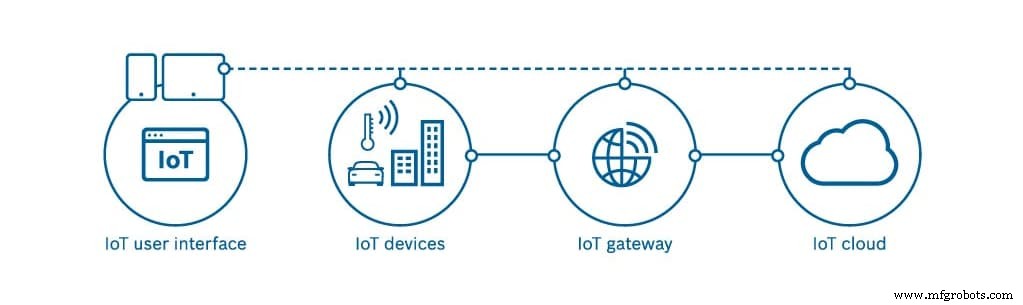
An IoT system typically comprises:
- IoT device
- Optional mobile device used to control the IoT device
- IoT gateway
- IoT cloud platform
“Unlike traditional computing devices, which have an expected lifetime of three to five years, an IoT device may be in use for decades.”
– Lorie Wigle, DarkReading.com
Because IoT devices can operate for decades, securing them is inherently complex. Effective oversight and procedures must be in place to address new vulnerabilities and threats, ensuring that the foundational mechanisms for remediation are already established. This demands a defined security lifecycle and robust privacy governance that remain compliant with data protection laws.
Implementing these practices guarantees that updates, patches, and configuration changes are performed safely and securely throughout the product’s lifespan.
Below is a short video that illustrates why security should be integrated from the very beginning of IoT design.
Watch the video: “Holistic IoT Security”
In our white paper, Holistic IoT Security, Bosch shares insights drawn from years of delivering connected solutions. We invite technology vendors to collaborate in setting high standards for IoT security and privacy, which is essential for building trust, accelerating market growth, and benefiting society.
Download the IoT security white paper
Internet of Things Technology
- Integrating Qt with DDS: Building Scalable IoT Applications
- AI & ML: The New Frontline in Cybersecurity
- How IoT Is Mitigating Security Risks in the Oil & Gas Industry
- SRAM PUF: The Ultimate Root of Trust for Secure IoT Devices
- New Testing Solutions Strengthen IoT Security for Faster, Safer Deployments
- Building Sustainable IoT Products: A Practical Guide for Product Leaders
- Bringing IoT to Life with IBM & Tech Data – Part 2
- Turning IoT Into Reality: Tech Data & IBM Insights – Part 1
- IoT-Driven Downtime Monitoring for Industrial Packaging Lines
- Industrial IoT Security: Overcoming Challenges and Implementing Robust Solutions



