SRAM PUF: The Ultimate Root of Trust for Secure IoT Devices
This article explains the fundamentals of SRAM Physical Unclonable Functions (PUFs) and demonstrates how they serve as the cornerstone of trust for Internet of Things (IoT) devices.
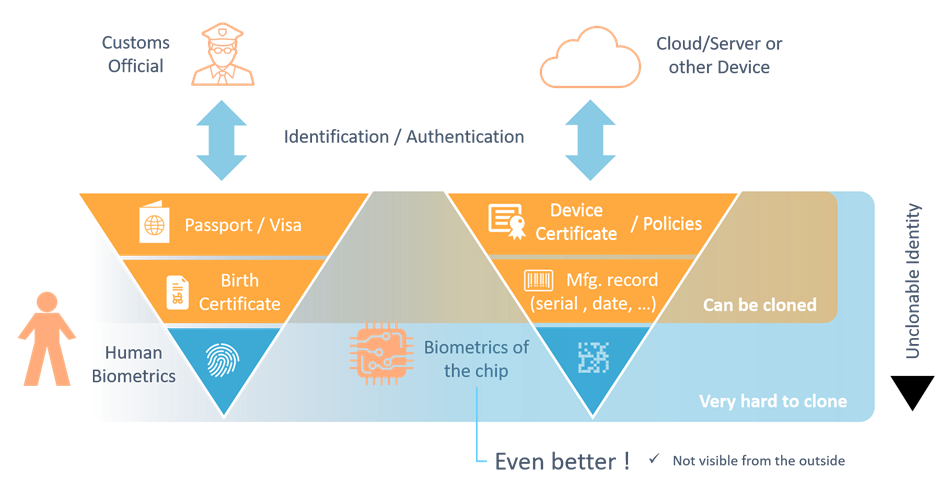
Trust is the bedrock of every security system. Whether you share an alarm code with a neighbor or a passport with a border checkpoint, you rely on a unique, unforgeable identifier. In the physical world, that identifier is often a biometric that cannot be copied. In the digital realm, the equivalent is a hardware‑based root key that cannot be cloned or extracted from the supply chain.
Physical Unclonable Functions provide precisely that anchor. They generate a device‑unique cryptographic key directly from the minute manufacturing variations that exist in every silicon chip. When this key protects certificates and keys, the device becomes a trustworthy entity in the IoT ecosystem.
Why SRAM PUFs Stand Out
Among the various PUF technologies, the SRAM PUF is favored for its reliability, scalability, and low integration cost. It can be activated simply by loading software onto an existing chip, eliminating the need for custom hardware IP blocks. This makes it ideal for billions of low‑cost IoT devices.
What Is an SRAM PUF?
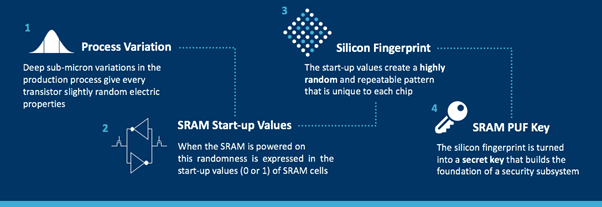
During semiconductor fabrication, tiny variations in transistor threshold voltages create a random, but repeatable, electrical signature in each SRAM cell. When the chip powers up, each cell settles into a preferred 0 or 1 state, producing a unique pattern—essentially a fingerprint for that silicon.
Because this pattern is inherently noisy, a Fuzzy Extractor is employed to reliably reproduce the same cryptographic key under varying environmental conditions. The result is a key that never resides in non‑volatile memory, thus eliminating the “key at rest” attack vector that plagues traditional storage methods.
Using SRAM PUFs as the Root of Trust
IoT devices need a secure foundation for keys that protect data, firmware, and communications. The SRAM PUF delivers this foundation by generating a root key within the silicon itself. OEMs can choose to pre‑provision this key or let the chip generate it during manufacturing—both approaches avoid costly, complex factory injection processes.
Unlike non‑volatile memory, which can be read by hardware attackers, the SRAM PUF’s key exists only in volatile registers and is regenerated on each power‑cycle. When combined with a secure element or the PUF’s own error‑correcting data, it forms a robust key vault that can support multiple application keys.

Building an SRAM PUF‑Based Key Vault
- Enroll: One‑time operation that generates the root key and stores non‑sensitive helper data in NVM. The root key never leaves the device.
- Start: Re‑creates the root key using the stored helper data and a fresh SRAM snapshot. The process fails if the helper data does not match the device.
- Wrap / Unwrap: Securely encrypts external keys into key codes (KCs) that can be stored unprotected. The KC can only be unwrapped on the originating device.
- Stop: Clears all sensitive data from registers before sleep or idle states, minimizing the attack surface.

Deriving Multiple Application Keys
Security best practice dictates that each application uses a distinct key. From the single SRAM PUF root, a cryptographically secure Key Derivation Function (KDF) generates numerous independent keys, ensuring that compromise of one does not weaken others. The KDF can produce keys of any length and structure required by different algorithms or lifetimes.
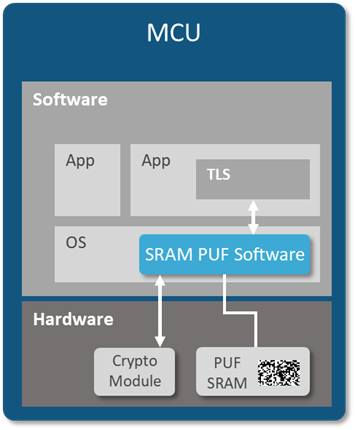
Implementing SRAM PUF in Software
Because SRAM is ubiquitous on virtually every digital chip, an SRAM PUF can be instantiated purely in software—no new silicon required. This feature enables remote, brownfield deployment of a hardware root of trust, expanding IoT security to billions of devices without redesigning hardware.
Conclusion
Trust is the foundation of all security. SRAM PUFs provide an unforgeable, device‑unique root key that is generated and stored entirely within silicon, eliminating supply‑chain risks and hardware attacks. Whether implemented as dedicated hardware or as software, the SRAM PUF forms a resilient root of trust, enabling secure key vaults and multiple application keys—protecting IoT devices from the ground up.
Internet of Things Technology
- Integrating Qt with DDS: Building Scalable IoT Applications
- Balancing Trust and Value in Industrial IoT: A Cisco Security Journey
- How IoT Is Mitigating Security Risks in the Oil & Gas Industry
- Secure IoT: Best Practices for Building Trustworthy Connected Products
- Strengthening IIoT Asset Tracking: Proven Security Practices
- Verizon and AT&T Deploy LTE‑M1 to Power Nationwide IoT Coverage
- U.S. IoT Security Law Sets New Standards and Liability Requirements
- Can Security and Privacy Hinder the IoT Revolution?
- Automation & IoT: Revolutionizing Healthcare Logistics & Security
- Memphis Goes Smart: Securing IoT, Visibility, and Control for a Resilient City



