New Testing Solutions Strengthen IoT Security for Faster, Safer Deployments
Rising cyber‑infrastructure threats from hostile actors are driving the development of advanced security testing tools for IoT software and hardware.
These innovations help embedded system developers meet the new security standards issued by the White House in response to recent high‑profile cyberattacks.
On the software side, a new application‑security test delivers mathematically proven, bug‑free code for embedded systems. TrustInSoft’s Analyzer transforms C/C++ source code into a mathematical twin, enabling exhaustive verification across all possible inputs. This approach guarantees the absence of source‑code bugs before the device reaches production.
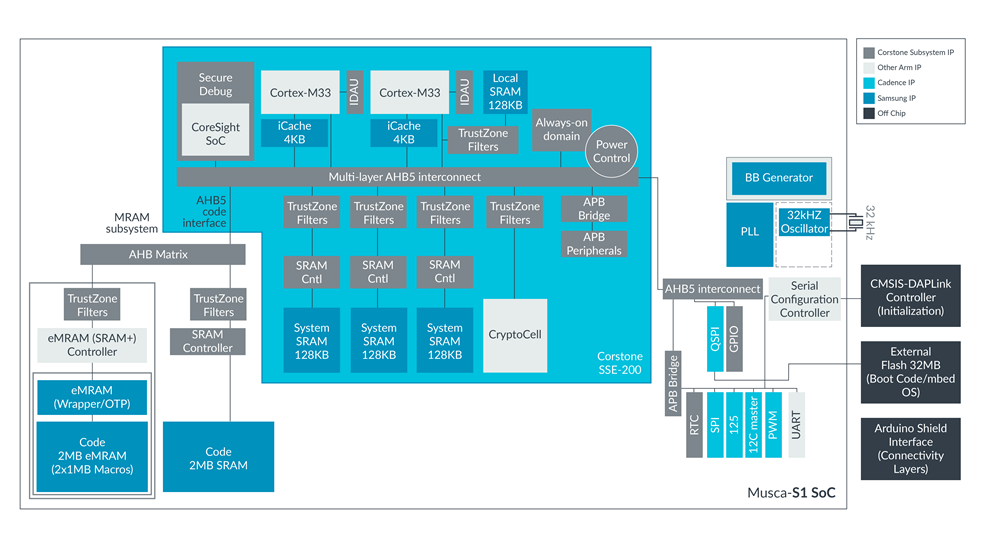
Figure 1: Analyzer automates formal methods to provide a synthetic view of source code bugs. Source: TrustInSoft
Traditional static and dynamic analysis methods duplicate testing for each process, slowing IoT design deployment. The new embedded IoT test, powered by TrustInSoft’s Analyzer, combines the rigor of static and dynamic analysis into a single, fast pass that verifies the absence of undefined behavior in C/C++ code.
TrustInSoft reports that the tool can reduce device rollout time by up to 40× and code verification time by up to 4×. Fabrice Derepas, founder and CEO, notes that a post‑release bug can cost up to 640× more than one discovered during development. “Life is never error‑free, but your source code can be,” he says.
On the hardware side, Arm has launched the Musca‑S1 IoT test chip and development board, a collaboration with Samsung Foundry, Cadence, and IC‑design services firm Sondrel. The platform uses a 28‑nm fully‑depleted silicon‑on‑insulator (FD‑SOI) embedded MagnetoResistive Random‑Access Memory (eMRAM) chip, offering advantages over traditional embedded flash memory and enabling scaling below the 40‑nm process node.
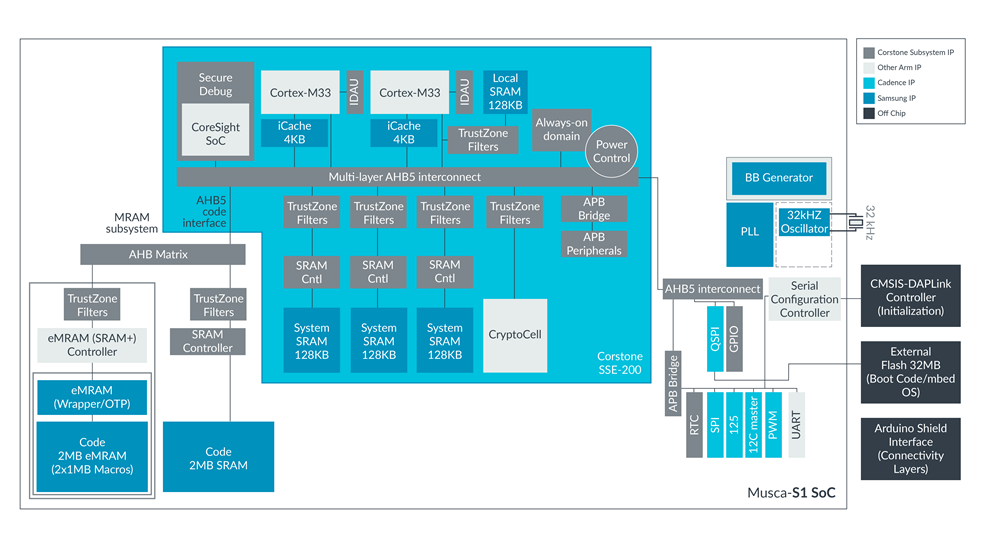
Figure 2: The Musca‑S1 embedded security test platform gives IoT chip designers more options. Source: Arm
By integrating these software and hardware testing solutions, IoT developers can prototype end‑to‑end security, accelerate time‑to‑market, and comply with essential cybersecurity guidelines.
>> This article was originally published on our sister site, EDN.
Internet of Things Technology
- Securing the Industrial IoT: A Practical Roadmap
- Secure IoT: Best Practices for Building Trustworthy Connected Products
- Four Critical IoT Security Threats in 2015 — What Developers Need to Know
- Two Essential Strategies for IoT Security
- IoT Security – A Practical Guide from Perry Lea
- Cypress Enhances IoT Security with PSA‑Certified PSoC 64 MCUs
- Securing IoT Embedded Designs with Advanced Security ICs
- IoT Security – Who Holds the Responsibility?
- IoT Security: Overcoming Deployment Barriers
- Industrial IoT Security: Overcoming Challenges and Implementing Robust Solutions



