Securing IoT Embedded Designs with Advanced Security ICs
Securing IoT Embedded Designs with Advanced Security ICs
In today’s connected world, every new smart device you develop carries the risk of becoming an attack vector. This article outlines the most pressing security threats for IoT designs, the essential functions that must be built in, and how modern security ICs simplify the task of protecting your product from the outset.
Why Timing Matters: From Copycats to Customer Harm
Security must be integrated early, not as an afterthought. Unprotected IoT devices can serve as gateways to corporate networks, jeopardizing sensitive data and, in some cases, user safety. Counterfeiting and cloning are common; they erode revenue and damage brand reputation. Genuine components not only guarantee performance but also help prevent malware infiltration.
High‑stakes examples include medical devices. A 2023 U.S. Department of Homeland Security advisory warned that a Wi‑Fi‑enabled pacemaker could be compromised by a short‑range attacker capable of injecting, replaying, or modifying telemetry data. Similarly, the FDA allows medical device refurbishing, but this process can undermine limited‑use features, creating additional risk.
Security ICs equipped with advanced cryptographic functions can shield IoT sensor nodes in critical infrastructures—such as power plants—from these threats.

Figure 1. Security ICs with advanced cryptographic features can protect IoT sensor nodes in power plants and similar applications from security threats.
Cryptography Made Accessible
Effective IoT security relies on four pillars:
- Secure communication and endpoint authenticity
- Robust key management for data encryption
- Secure boot to validate firmware and block malware
- Feature control for safe enablement/disablement of factory options
Security ICs embed these capabilities, allowing designers to leverage industry‑grade cryptography without deep expertise. A purely software approach demands extensive development and can introduce exploitable vulnerabilities.
Physically Unclonable Function (PUF) Technology
PUF technology generates unique cryptographic keys on the fly, drawing on the inherent randomness of MOSFET devices. Because the key is never stored, an attacker cannot extract it. Moreover, probing a PUF alters its behavior, thwarting reverse engineering.
PUFs act as a hardware fingerprint, ideal for securing keys used to encrypt EEPROM contents. Even if an attacker reads the memory, decryption is impossible without the PUF‑derived key.
Symmetric and Asymmetric Algorithms
Symmetric algorithms use a single shared secret key, while asymmetric schemes employ a private/public key pair. Both are essential: symmetric keys provide fast bulk encryption, whereas asymmetric keys enable authentication and digital signatures.
Advanced Encryption Standard (AES)
AES is the industry standard for bulk encryption. It processes 128‑bit blocks through a series of substitution, permutation, and XOR operations driven by a secret key. The same key is used for encryption and decryption, ensuring data confidentiality.
Digital Signatures for Trust
Digital signatures confirm that a message originates from a known sender and remains untampered. Both symmetric and asymmetric algorithms can produce signatures, with asymmetric schemes (e.g., ECDSA) offering higher assurance.
Secure Boot with SHA and ECDSA
Secure boot verifies firmware integrity before execution. In practice, the firmware’s SHA‑256 hash is calculated, then signed with an ECDSA private key stored securely in the development environment. The signed firmware and the public key are embedded in the device’s flash. Upon boot, the microcontroller recomputes the hash, verifies the signature using the public key, and only then runs the firmware.
Modern security ICs integrate SHA‑256, ECDSA, and key‑exchange mechanisms, allowing a low‑power cryptographic coprocessor to offload complex operations from the host microcontroller.
An example is the DS28S60: a low‑power 20 MHz SPI coprocessor featuring PUF, SHA‑256/ECDSA‑P256 for secure boot, and built‑in key‑exchange for end‑to‑end encryption.
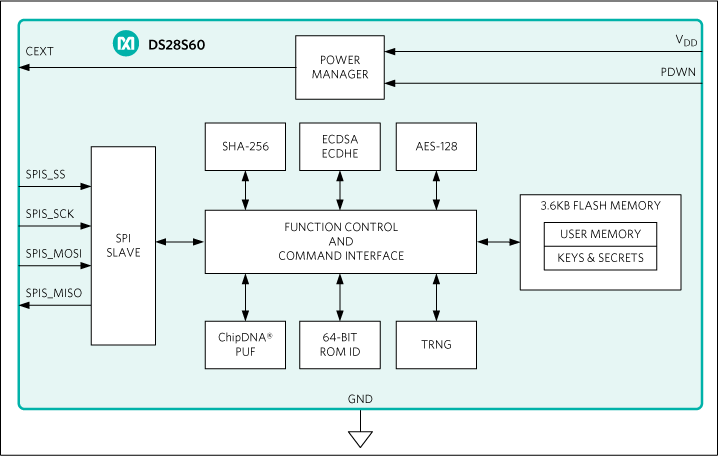
Figure 2. DS28S60 simplified block diagram
Takeaway
As battery‑powered IoT sensor nodes become ubiquitous, embedding robust security from the start is non‑negotiable. Today’s security ICs provide a comprehensive suite of cryptographic functions—PUF, AES, SHA, ECDSA—enabling designers to protect their products without becoming cryptography experts.
This article was co‑authored by Zia Sardar and Nathan Sharp of Maxim Integrated.
Industry Articles are a form of content that allows industry partners to share useful news, messages, and technology with All About Circuits readers in a way editorial content is not well suited to. All Industry Articles are subject to strict editorial guidelines with the intention of offering readers useful news, technical expertise, or stories. The viewpoints and opinions expressed in Industry Articles are those of the partner and not necessarily those of All About Circuits or its writers.
Internet of Things Technology
- Two Essential Strategies for IoT Security
- New Testing Solutions Strengthen IoT Security for Faster, Safer Deployments
- IoT Security Services Market to Reach $8 B by 2026 Amid 5G Expansion
- IoT Security – A Practical Guide from Perry Lea
- Cypress Enhances IoT Security with PSA‑Certified PSoC 64 MCUs
- Maxim Integrated Launches DS28E38 Secure Authenticator Using ChipDNA PUF for Unmatched IoT Protection
- Six Proven Steps to Secure Embedded IoT Systems
- Industrial Control Systems Face Elevated Cyber Risk Amid U.S.–Iran Tensions
- Industrial Control Systems at Risk Amid US‑Iran Tensions
- 8 Key Security Challenges Facing Industrial IoT



