MCUs Harness PUF Technology to Bridge the Private Key Security Gap
More integrated‑circuit vendors are turning to physically unclonable functions (PUFs) as a device‑level security strategy. While semiconductor processes are highly precise, each silicon die still exhibits minute, inherently random variations. A PUF captures these variations to generate a unique digital value that serves as a secret key—an essential component of modern cryptographic systems.
Security has become a paramount concern for developers of connected, or Internet‑of‑Things (IoT), devices. Hackers and data‑breach incidents threaten the integrity and privacy of millions of deployed units worldwide.
Adding robust security to an IoT device is challenging because manufacturers must avoid increasing silicon area or cost while maintaining ultra‑low power consumption and efficient processing. PUFs address these constraints by eliminating the need for dedicated key storage hardware.
PUF circuitry requires no permanent power source. Any attempt to probe the key physically alters the circuit’s characteristics, causing a different output value. Consequently, the key is generated on‑demand for cryptographic operations and erased immediately afterward, making it virtually impossible to extract.
Because PUFs can replace traditional key vaults, they reduce bill‑of‑materials (BOM) complexity while offering tamper‑resistant protection comparable to secure SRAM. Though PUFs alone do not guarantee absolute key security, they dramatically lower the attack surface for embedded devices.
Recent product launches from Maxim Integrated and Silicon Labs demonstrate how PUFs are being integrated into secure microcontrollers and system‑on‑chip (SoC) solutions. Silicon Labs’ Wireless Gecko Series 2 SoCs incorporate an SRAM‑based PUF that generates a device‑unique symmetric key. Maxim Integrated’s MAX32520 ChipDNA Secure ARM Cortex‑M4 MCU embeds a PUF that produces a ChipDNA key used for encrypting non‑volatile memory, securing firmware, and enabling secure boot.
A Maxim spokesperson told EE Times that the MAX32520 “is not limited to IoT; it also serves industrial, healthcare, and computing applications.” The MCU’s architecture includes serial flash emulation, die shielding, and tamper‑detection circuitry. It supports robust cryptographic primitives—SHA‑512, ECDSA‑P521, and RSA‑4096—and leverages the ChipDNA key to encrypt all stored data, including user firmware, thereby protecting intellectual property.
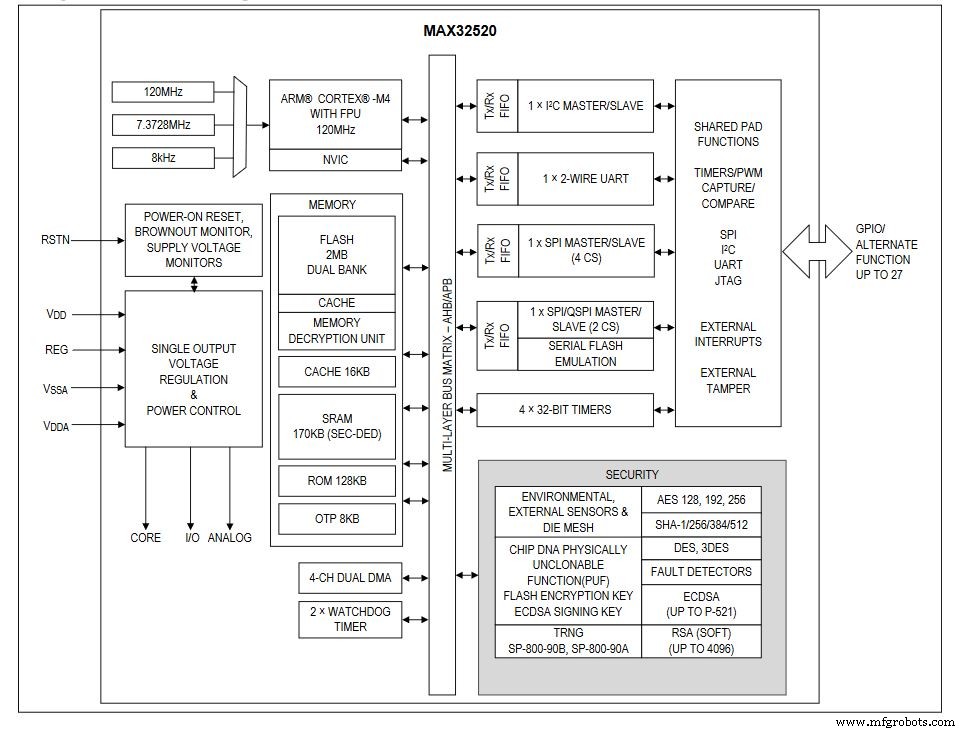 Simplified block diagram of Maxim’s ChipDNA microcontroller (Image: Maxim Integrated)
Simplified block diagram of Maxim’s ChipDNA microcontroller (Image: Maxim Integrated)
The ChipDNA can also serve as a private key for ECDSA signing. The MAX32520 offers a FIPS/NIST‑compliant true random number generator, environmental monitoring, and tamper detection, all of which contribute to a robust system‑level security stack. Any attempt to observe or probe the ChipDNA circuit modifies its characteristics, thwarting reverse engineering efforts.

Mike Dow, Silicon Labs
Silicon Labs’ senior product manager for IoT security, Mike Dow, explained how the company employs a SRAM‑based PUF in its secure vault and secure element technologies. The SRAM PUF exploits the inherent randomness of SRAM bits at power‑up to generate a single, device‑unique symmetric key. The team selected SRAM PUF because it has the longest proven reliability record—critical for devices that may operate for over a decade in the field.
In the Silicon Labs design, the PUF is used exclusively to generate a Key Encryption Key (KEK) that wraps other keys stored in internal or external memory. Because the KEK is only active during a power‑on reset, its exposure window is minimal, reducing attack surface. The reconstruction of the KEK occurs only on POR events, further limiting access.
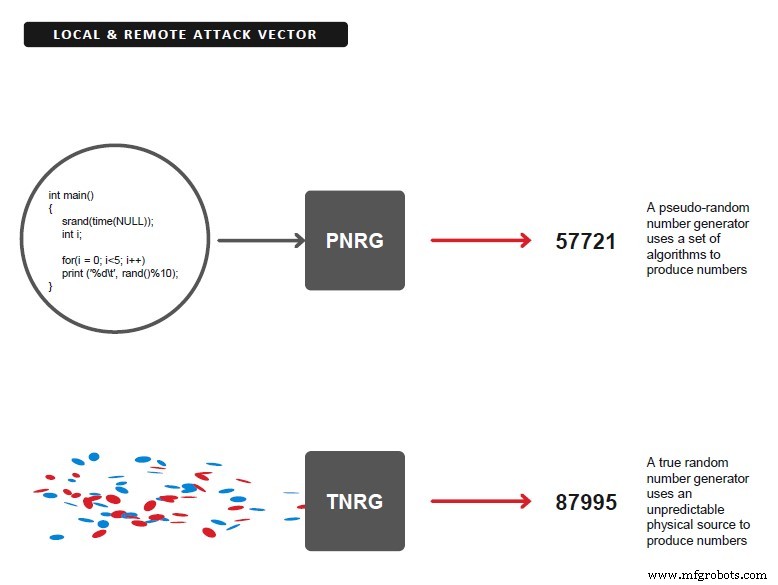 In Silicon Labs design, every other key generation besides the key encryption key is performed by a NIST‑compliant true random generator (TRNG). (Image: Silicon Labs)
In Silicon Labs design, every other key generation besides the key encryption key is performed by a NIST‑compliant true random generator (TRNG). (Image: Silicon Labs)
All non‑KEK key material is generated by a NIST‑compliant TRNG and wrapped with AES‑256 encryption. The use of a 256‑bit key, combined with differential power analysis (DPA) side‑channel protection, ensures that the AES implementation resists advanced cryptographic attacks. Key material—including ECC private/public identity key pairs—is stored in one‑time programmable (OTP) memory, preserving confidentiality even if the device is physically compromised.
The ability to store vast amounts of key material securely in internal or external memory is a decisive advantage for implementing complex cloud security schemes that require multiple asymmetric key pairs. Storing keys in plain text would necessitate physically secure memories, which are costly and difficult to protect.
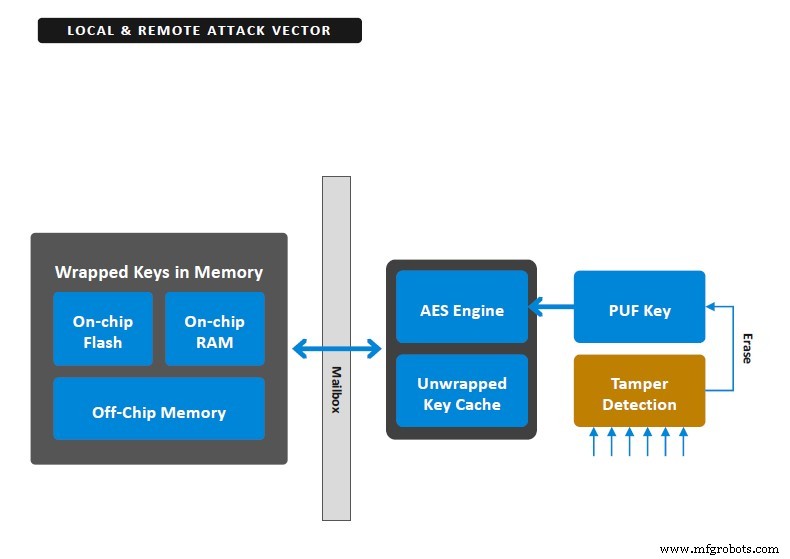 A PUF creates a secret, random and unique key; the PUF‑key encrypts all keys in the secure key storage, generated at startup and not stored in flash. (Image: Silicon Labs)
A PUF creates a secret, random and unique key; the PUF‑key encrypts all keys in the secure key storage, generated at startup and not stored in flash. (Image: Silicon Labs)
Silicon Labs enhances its secure vault by requiring an initial vector (IV) to feed the AES algorithm. The IV acts like an additional 128‑bit password, enabling two‑factor authentication—either by a human operator or another application running on the chip—to access the key.
Furthermore, the secure vault includes a sophisticated tamper‑protection scheme that can erase the PUF reconstruction data if a tamper event is detected. Once erased, the stored key material becomes inaccessible, effectively “bricking” the device and preventing any further cryptographic operations, including secure boot.
By selecting the most reliable PUF technology on the market and limiting its role to generating a single KEK, Silicon Labs ensures that even if an attacker compromises a device, the impact is confined to that device alone. Additional tamper‑protection sources can destroy the PUF key, rendering all wrapped keys useless. When combined with two‑factor authentication and a robust AES implementation, this strategy delivers strong, layered security for connected devices.
Embedded
- Cortex‑M33 Microcontrollers Elevate IoT Security with TrustZone
- IoT Security and Fragmentation Remain Top Challenges, GSMA Survey Reveals
- IoT Security: Cryptographic Foundations for Robust Device Protection
- Microchip & The Things Industries Deliver End‑to‑End LoRaWAN Security for Trusted Key Provisioning
- Cypress Unveils PSoC 64 Secure MCUs: PSA‑Certified, Arm Cortex‑M, Ready for IoT Security
- STM32H7 MCUs: 280 MHz Cortex‑M7, Advanced Connectivity, & Robust Security
- MAX32520: A Secure ARM Cortex‑M4 Microcontroller Leveraging ChipDNA PUF Technology
- PUFrt: First Quantum‑Tunneling PUF IP Enhances IoT Security with Unmatched Stability
- CrossBar Pioneers ReRAM‑Based PUF Keys for Next‑Gen Hardware Security
- Discover Your Network Security Key: Easy Steps to Find and Protect Your Wi‑Fi



