The Hidden Cost of Inaction: Protecting Your Manufacturing Plant from Cyber Threats
Source: Edreformnow.org
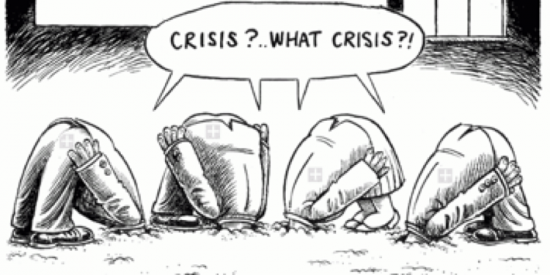
When you tell your team, “Upgrading our equipment is too expensive and likely to cause downtime. Let’s just keep it running,” you’re making a risk decision. Cybersecurity has historically been a low‑profile concern, but today it ranks among the top threats to manufacturing operations.
Risk management in manufacturing typically balances cost against safety. Costs include downtime, intellectual‑property theft, counterfeiting, brand erosion, personal injury, and even loss of life. Moreover, large‑scale cyber attacks trigger mandatory reporting on SEC filings, adding regulatory pressure.
Outdated systems and limited security expose plants to uncontrolled failures—complete process crashes, power outages, or worse, physical harm to personnel. A 2014 incident in Germany saw a blast furnace hacked, causing tens of millions in damage without injuries, yet the financial toll was staggering.
Many manufacturers are now adding cyber‑attack coverage to their insurance portfolios. While insurance mitigates financial loss, it is inherently reactive and simply the cost of doing nothing. A comprehensive strategy must combine robust insurance with proactive measures that eliminate or mitigate plant‑floor attack vectors.

Locking down the factory and restricting connectivity would render a business uncompetitive in the connected economy. So how can you stay safe while embracing IoT, external connectivity, and machines as a service?
Consider these actionable steps:
- Upgrade legacy equipment and control systems to support modern virus and malware defenses. If a full upgrade isn’t feasible, impose strict controls on legacy assets and mandate that new automation meets elevated cyber‑security standards.
- Eliminate USB drives everywhere on the manufacturing floor.
- Virtualize shop‑floor PCs and industrial computers to reduce unplanned outages and enhance security.
- Implement edge‑compute capabilities through centrally managed industrial switching platforms.
- Deploy firewalls and identity‑management technologies to manage, control, and audit access to factory‑floor networks.
- Partner with leading security firms—at Cisco we employ over 5,000 cybersecurity experts.
- Adopt platform‑based solutions built on secure, pre‑integrated modular platforms. While cutting‑edge startups may promise innovation, their integration costs, vendor stability, and rapid obsolescence pose significant business risk.
For a deeper dive, the National Institute of Standards and Technology (NIST) has released a draft Manufacturing Cyber‑Security Profile that outlines a framework for identifying, protecting, detecting, responding to, and recovering from cyber incidents.
Our whitepaper, Holistic Security for the Factory of Tomorrow, explores these topics from both business and technology perspectives.
If you’d like to discuss security strategies for your plant, reach out to me at neheller@cisco.com. I look forward to learning about your goals and exploring how we can help. Special thanks to colleagues Steve Marchewitz, Pat Mitchell, and Greg McCarthy for their insights.
For more information on factory security:
Internet of Things Technology
- The Security Seven: 7 Proven Strategies to Protect Your Factory from Modern Threats
- Securing the Industrial IoT: A Practical Roadmap
- Two Essential Strategies for IoT Security
- Designing Security into the Industrial IoT: Expert Guidelines for Protecting IIoT Systems
- Securing the Internet of Things: The Product Manager’s Imperative
- Securing Your IoT Ecosystem: Expert Strategies to Counter Ransomware and Cyber Threats
- IoT Device Adoption Fuels Rising Cybersecurity Threats: What Governments Must Do
- ETSI’s EN 303 645: Are Regulators Adequately Protecting IoT Devices?
- Security Unlocks IoT’s Full Potential
- Understanding the Security Industry: Products, Services, and Global Impact



