Essential Security Practices for Fog Computing
For several years, Cisco has championed Fog Computing as a cornerstone of scalable, reliable, and cost‑effective IoT architectures. By integrating Cisco IOx into industrial IoT solutions, data generated by connected devices can be filtered, analyzed, and acted upon directly on edge routers and switches. This local processing introduces new security challenges that must be addressed across the entire Fog ecosystem, from individual IIoT devices to the thousands of Fog nodes that may be deployed in a production environment.
Security in Fog Computing is not a single feature or protocol—it is a layered architecture that requires solid foundations, much like building a sturdy house. By combining best practices for Cisco IOS network services with Cisco IOx security throughout each phase of a Fog rollout (see Figure 1), organizations can establish a resilient security posture.
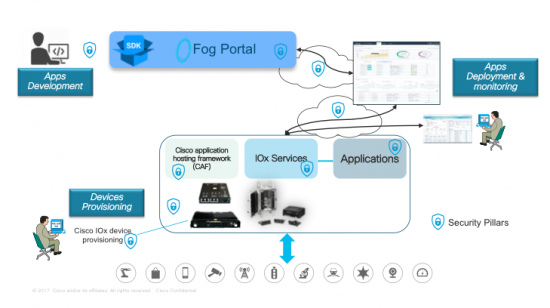
Below are four security pillars that help IT and operations managers safeguard data integrity in a Fog environment.
Cisco IOx Security Pillars
 Access control
Access control
Deploying and managing applications in Fog requires role‑based authentication that separates network management from application management.
- Application managers authenticate through Fog Director or IOx Local Manager (e.g., application install, upgrade, start/stop, validation, and monitoring). Enterprise Radius servers enforce login restrictions to block unauthorized access.
- Privileged IOS network managers perform device provisioning, interface configuration, and troubleshooting based on their role, not on login credentials or physical location.
 Integrity
Integrity
Beyond the hardware and software hardening discussed in [hardening], Fog computing demands additional safeguards to protect the IOx platform:
- Digitally signed Guest‑OS images, secured by the Trust Anchor Module (TAM) in Cisco ACT2 chipsets, verify OS integrity.
- Application isolation—whether as Docker containers, PaaS, Linux containers, or virtual machines (CGR 1000 Compute module only)—protects resources from interference.
- Signed application packages use a Trust Anchor RSA private key (PEM) and an x509 client certificate (PEM) to confirm source identity. All IOx tools (IOxclient, IOx Local Manager, Fog Director) enforce the installation of signed apps to prevent rogue code.
- OAuth APIs provide delegated access, authenticating users without exposing credentials to applications.
- PAM allows developers to integrate multiple low‑level authentication schemes via a high‑level API.
 Data confidentiality and privacy
Data confidentiality and privacy
Fog nodes often store data locally on embedded flash or mSATA SSDs (e.g., IR829M). Recent IOx releases introduce Secure Storage Services (SSS) that safely store certificates, keys, and user data. Applications access SSS via REST APIs, enabling application‑level encryption. Linux security mechanisms such as Cgroups, SMACK, SELinux, and Namespaces provide additional layers of protection.
Control commands (start/stop, install/uninstall) must also remain confidential. SSL/TLS secures traffic between Fog devices and management services, including file transfers. Complementary Cisco IOS configurations—IPsec VPNs, VRFs, VLANs—further isolate data traffic.
Threat detection and mitigation
Distributed traffic analysis is a core feature of Fog computing. Partners such as [Sentryo] leverage port mirroring on IE 4000 Series or IP traffic export on IR800 Series to deliver analytics agents that monitor traffic flows on IOx devices.
Operations managers need to detect anomalous application behavior and capture metrics for analysis and capacity planning. IOx Local Manager and Fog Director tools/APIs profile application resource consumption, while DNA‑C, IoT FND, and Kinetic GMM automate provisioning and policy enforcement across thousands of IOx devices.
Share your security challenges with us—visit the Cisco Live Orlando World of Solutions and IOx Devnet Zone from June 10–14, 2018 to discuss how to secure your Fog deployment.
Internet of Things Technology
- Mastering Synthetic Monitoring: Proven Best Practices for Reliable SaaS & Web Performance
- How to Debug Zephyr‑Based IoT Devices: Proven Remote‑Monitoring Practices
- How Face‑Time Coaching Transforms Maintenance Supervision
- 12 Proven Practices for a Successful CMMS Implementation
- Mastering Aluminum Welding: Proven Techniques for Strong, Reliable Joints
- Robotic Welding Best Practices: Boost Quality, Speed, and Savings
- Top 6 Proven Strategies for Accurate Warehouse Inventory Tracking
- Top 4 Fixed Asset Tracking Best Practices for Business Efficiency
- Manufacturing Marketing: Proven Best Practices for 2019 Success
- Multi‑Cloud Security: Proven Best Practices for Safeguarding Your Data



