







Industrial Technology

Researchers designed magnetic nanostructures with an invisibility cloak. High speed of tiny magnetic bit structures can be achieved by carefully adjusting the strength of the invisible cloak. For high-performance solid-state data storage and logic applications, researchers are focusing on spin-
New deep learning model analyzes breast tissues in mammograms and accurately estimates density ratings. These ratings are an independent risk factor for breast cancer. The model takes less than one second to process one mammogram and it could be easily scaled throughout hospitals. In the Unite
For the first time, researchers develop a technique to capture 3D images of microscopic cracks in nickel-base alloys caused by hydrogen or water exposure. It will help engineer develop microstructures with extended material life, saving costs on repairs and replacements. Microfractures in metal
Researchers want to blast holes in the clouds to transmit information at high rates. To do this, they will use ultrashort high-intensity laser filaments. The technology doesn’t leave any negative impact on the atmosphere. Today’s long-range information is transmitted by either radio waves (vi
New model examines how infectious seeds diffuse through the uneven structure of the brain. Researchers used MRI scans of an adult brain to create high-resolution simulations in both 2D and 3D. These simulations recreate the pattern of damage observed in numerous neurodegenerative disorders. Neu
The number of security threats is increasing day by day, making high speed wired/wireless network insecure and unreliable. According to the study conducted at the University of Maryland, hackers attack internet-connected devices every 39 seconds on average, affecting one-third of Americans every ye
In today’s corporate world, security has become the most common issue. Every day, we hear about how attackers hacked computer systems and stole all crucial information. In 2019, there were 1,473 reported data breaches in the United States, with more than 164 million sensitive records exposed. In th
Cloud computing is the delivery of various services via the Internet. These services include servers, networking, databases, storage, software, analytics, and intelligence. In other words, cloud computing transforms IT infrastructures into a utility. You can connect to infrastructure through the In
Technology is about more than just gadgets and gizmos. It has a very broad and deep definition. The term “technology” comes from the Greek word “teckne” (which relates to art or craft) and “logia” (which relates to study). The combination of these two words, teknologia, means systematic treatment.
In the field of Information Technology, systems design involves the process of determining the architecture, interfaces, modules, and data for a system to fulfill certain requirements. It’s a crucial process for improving product/service development efficiencies and enabling a great user experience
A data center is a physical facility that private companies and governments use to store and share applications and data. Most businesses depend on the data center’s reliability and security to run their IT operations optimally. However, not all data centers are the same: their design is based on s
NEMS (short for NanoElectroMechanical System) are devices that integrate electrical and mechanical functionality at the nanoscale, i.e., at or below 100 nanometers. They are the advanced level of miniaturization after MEMS (MicroElectroMechanical System) that usually deals with components between 1
Data science is a multidisciplinary field that uses scientific techniques and computational algorithms to collect valuable insights and knowledge from structured and unstructured data. It involves mathematics, statistics, statistical modeling, computer science, database technologies, programming, p
A computer virus is a malware program that is written intentionally to gain access to a computer without its owner’s permission. These kinds of programs are primarily written to steal or destroy computer data. Most systems catch viruses due to program bugs, the vulnerability of operating systems, a
Software as a Service (SaaS) companies are growing at a phenomenal rate these days, thanks to the advances in cloud computing technologies. They host applications in the most efficient way and make them available to customers over the Internet. B2B SaaS refers to companies that provide software (ap
Malware (also known as malicious program) is any piece of program that is written with the intent of doing harm to devices and data. It is created with an objective in mind. While the objective is limited only to the imagination of its creator, most malicious programs are written to steal data, cre
Quantum finance is a branch of econophysics, a heterodox interdisciplinary research field that involves applying theories and techniques to solve complex problems in economics. Implementing quantum technology to financial problems — especially those dealing with nonlinear dynamics, uncertainty, or
Exploring IEC 61851: The Four Key EV Charging Modes Global electric‑vehicle adoption hinges on robust international standards that ensure safety, reliability, and seamless interoperability. The IEC 61851 standard, focused on conductive charging systems, defines four distinct charging modes—1 through
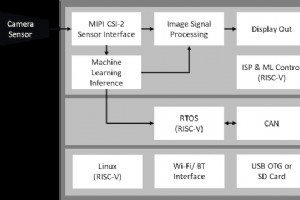
This article demonstrates how a Trusted Execution Environment (TEE) combined with a secure FPGA SoC can protect in‑cabin AI systems in modern vehicles. Part I of this series, Trusted Execution Environments in Connected Cars, explained that while TEEs are ubiquitous on smartphones, their adoption in

Semiconductor Innovations Powering Faster, Safer, and High‑Efficiency EV Chargers As electric‑vehicle fleets grow, the demand for charging infrastructure that delivers power quickly, reliably, and with minimal losses has never been higher. Modern EVs feature larger battery packs that require fast DC
Industrial Technology
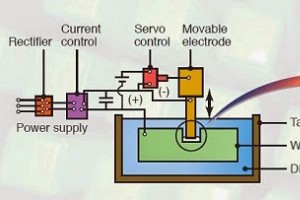
Electrical Discharge Machining (EDM): Principles, Process, Equipment, Pros & Cons Explained
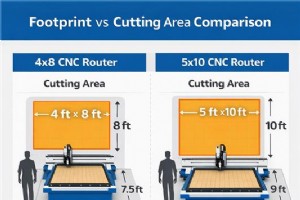
4×8 vs 5×10 CNC Router Beds: Which Size Drives Your Business Success

Microwave PCB Design: The Ultimate Solution for High‑Frequency Applications

U.S. Customers Celebrate Successful Delivery of Blue Elephant CNC Engraving Machine