RFID‑Based Home Security: Low‑Cost, Battery‑Free Monitoring Solutions
To meet contemporary homeowner expectations, modern security solutions prioritize wireless monitoring of the entire residence—covering perimeter protection, intrusion alerts, and safeguarding sensitive zones like medication cabinets, safes, and hidden valuables.
Video surveillance can detect unauthorized activity, but it demands complex image processing and raises privacy concerns. Conventional motion sensors sidestep privacy issues yet depend on power supplies and electronics that inflate BOM costs. They also require wired or wireless links to relay data to the cloud, often necessitating professional installation—prohibitive for budget‑conscious users.
This article explores a cost‑effective, battery‑free alternative that many consumers and small businesses can adopt: RFID tags as the backbone of lightweight, plug‑and‑play home security.
RFID tags can serve as the foundation for a range of robust security sensors. By integrating a reed switch, an RFID tag can detect motion; swapping the reed for a shock switch enables a vibration detector. In both configurations, the switch bridges the antenna and the RFID chip, turning the tag’s operation on or off depending on the switch state.
These compact sensors offer a low‑cost solution illustrated in Figure 1. RFID tags equipped with motion sensors can be mounted on windows, doors, and safes, while a shock‑sensing tag can secure a medication box. A commercial RFID reader performs two functions: (a) it detects any sensor that transitions to its active state, and (b) it emits low‑power RF radiation that powers the tags when activated. Because each tag has a unique ID, the reader knows exactly where the event occurred. The data can then be sent to the cloud for analysis and, if necessary, trigger a smartphone notification or email alert.
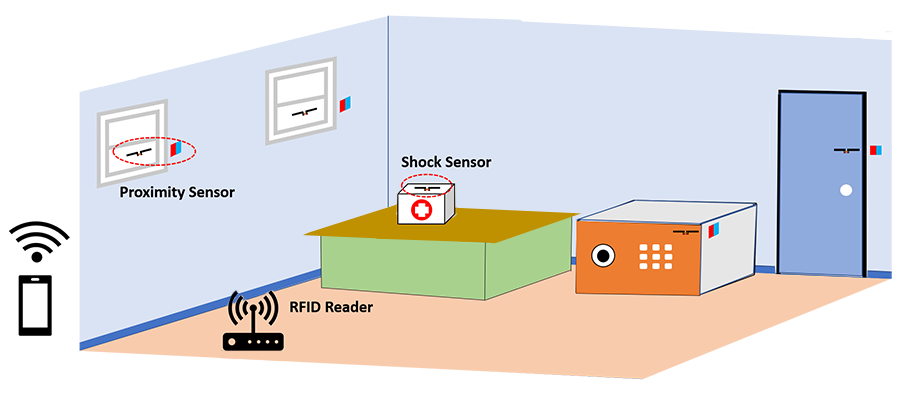
Figure 1. Security monitoring using RFID tag.
Sensor working principles
The functional diagrams in Figure 2 illustrate the working mechanisms of the shock sensor and motion sensor.
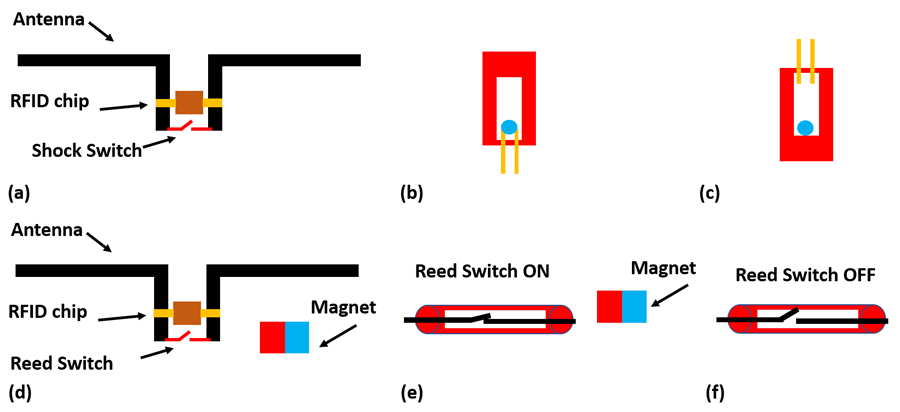
Figure 2. A shock sensor is comprised of an RFID chip, an antenna, and a shock sensor (a). In its normal (undisturbed) state, the metal ball shorts the two contacts of the shock sensor (b). When the sensor is disturbed, its metal ball no longer shorts the two contacts, allowing the antenna to receive power for the RFID chip, and to transmit its signal (c). A motion sensor is composed of an RFID chip, an antenna, and a reed switch (d). In its normal state, the reed switch is held in its ON state by a magnet affixed nearby. This shorts the antenna, preventing the RFID chip from receiving power (e). When the magnet is removed, the reed switch transitions to its OFF state, thereby enabling the RFID device (f).
Shock detector
The shock sensor consists of an RFID chip and an antenna, as shown in Figure 2a. The shock switch features a cavity and a tiny metal ball that rolls inside. When positioned upright, the ball contacts two conductive pads, completing a circuit (Figure 2b). Tilting the sensor separates the contacts, providing a simple means to detect motion or orientation. When used as a security sensor, the shock switch is wired between the antenna terminals and placed upright, shorting them in its passive state. This short disrupts the antenna’s impedance match, preventing the RFID chip from radiating. Tilting the sensor disengages the contacts, enabling the tag to receive power and transmit its signal, which the reader then captures.
Motion sensor
The motion sensor comprises an RFID chip, an antenna, a reed switch, and a magnet. The reed switch contains two ferromagnetic contacts sealed in glass. In the presence of a magnetic field, the contacts close (Figure 2e). Removing the magnet opens the contacts (Figure 2f), allowing the RFID chip to power up and alert the reader that the tag has moved. In practice, a tag mounted on a window is kept active by a magnet attached to the adjacent wall. When the window opens, the magnet’s influence wanes, the reed switch opens, and the tag becomes active, signaling the reader.
Dumb sensors, smart system
Because each RFID tag carries a unique identifier, the reader can map the signal to a specific location or object. This mapping lets the cloud‑based application interpret the event—identifying potential intruders, their positions, and inferring their actions. Such intelligence also reduces false alarms from pets or benign disturbances.
RFID technology offers a promising path to robust, reliable, and inexpensive security solutions. Tags are easy to install, battery‑free, and durable over the long term. Successful deployment, however, requires careful placement of readers to ensure full coverage and the development of smart readers that can perform preliminary data filtering and event classification.
>> This article was originally published on our sister site, EDN.
Embedded
- Active vs Passive RFID for Asset Tracking: 2021 Expert Guide
- mmWave Radar for Contactless Monitoring of Heart and Breath Rates
- RFID Explained: Boosting Asset Tracking with Radio‑Frequency ID
- Industrial IoT Monitoring: Essential Hardware Components and Setup Guide
- Smart Home Monitoring Powered by Alexa
- Advanced Self‑Heating Wearable Gas Sensor for Precise Health and Environmental Monitoring
- Six Innovative Metrics to Measure Automated Incident Response Effectiveness
- Critical Limitations of RFID in Military Asset Tracking
- RFID in Inventory Management: Advantages, Challenges, and ROI Insights
- Affordable Desktop CNC Machines for Precision Metal Cutting at Home



