Identifying and Mitigating Privacy Risks in Embedded System Design
Embedded devices are increasingly ubiquitous, but each new Internet‑connected product brings fresh privacy concerns. Fortunately, a growing portfolio of off‑the‑shelf silicon and software services can help designers build resistance against intrusion and unauthorized data exposure. The first step is to pinpoint the exact threats that must be mitigated.
In practice, privacy means preventing any party—except an authorized owner—from accessing specific information. While privacy is a subset of security, the two are distinct. Security also guards against malicious modification or destruction of data. A system can be secure without being private, but a private system must be secure.
Regulatory frameworks worldwide—such as GDPR, CCPA, and numerous national laws—mandate the protection of personally identifiable information (PII). Classic PII includes names, addresses, account numbers, locations, health data, images, and activities. Yet not all sensitive data is obvious PII. For example, a thermostat’s temperature setting alone is harmless, but when combined with the device’s location it becomes personally identifiable. Knowing that a particular home’s thermostat reads 55 °F could signal that the occupants are away, making the property a burglary target.
Embedded products store and transmit vast amounts of data—both at rest (in memory or flash) and in transit (across buses, networks, or even on PCB traces). Protecting this data typically requires encryption, which in turn mandates safeguarding the encryption keys. In addition, firmware and operating systems must be hardened against tampering; otherwise, a compromised microcontroller could deliberately leak sensitive information.
Attack vectors are diverse. Remote adversaries can eavesdrop on network traffic, perform man‑in‑the‑middle (MITM) interceptions, or inject malicious code via over‑the‑air updates. Physical adversaries, or even those merely in proximity, can probe signal lines, monitor power consumption or electromagnetic emanations to recover keys, replace storage media, or remove protective packaging for die‑level inspection.
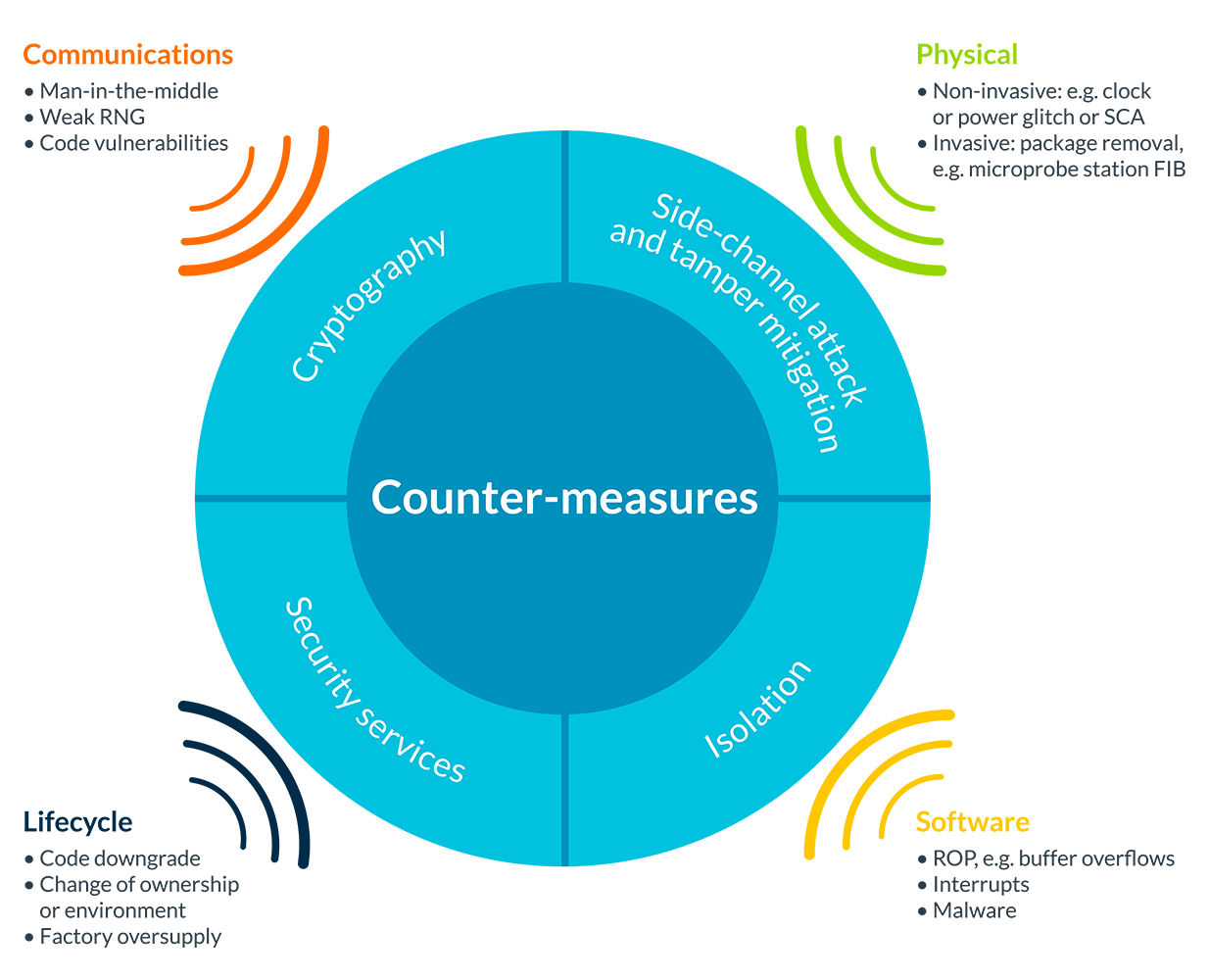
Figure 1: There are many forms of attack that can compromise data security, requiring many different countermeasures. (Image source: ARM)
Manufacturing stages also pose risks. During assembly, attackers can duplicate encryption keys or clone entire devices, allowing the replica to infiltrate a network undetected. At end‑of‑life, discarded hardware can be salvaged and probed to retrieve stored secrets.
No single defense covers every threat, and deploying all possible safeguards can be cost‑prohibitive. Attack likelihood and impact vary by application, so designers must prioritize measures that offer the greatest risk reduction for their specific context. The starting point is a thorough threat model built before detailed design begins.
Developing an effective threat model involves three key steps:
- Identify assets. For privacy, this includes all PII that may reside on or travel through the device, encryption keys, firmware, identity codes, message metadata, and related resources.
- Assess threats. Enumerate potential attack vectors, estimate their probability, and evaluate the impact of a successful compromise. Consider the full device lifecycle—from manufacturing and deployment to disposal—to capture all relevant risks.
- Determine countermeasures. Match each threat with appropriate mitigations and evaluate their implementation cost, performance overhead, and bill‑of‑materials impact.
With a well‑defined threat model, designers can tailor hardware and software features—such as secure boot, tamper‑evident packaging, side‑channel countermeasures, and robust key‑management—to protect privacy effectively. The semiconductor ecosystem now offers a rich set of silicon blocks, security modules, and software libraries that address most common attack vectors, and vendor support is available to help select and integrate the right solutions.
By systematically identifying assets, evaluating threats, and applying targeted countermeasures, developers can build embedded systems that meet both regulatory obligations and users’ expectations for privacy and security.
Internet of Things Technology
- Advancing Microelectronics to Meet AI's Evolving Demands
- Securing Smart Meter Lifecycles: Six Proven Strategies for Privacy and Resilience
- Unlocking AI Value with Unlabeled Data: How Hologram Stress‑Tests Autonomous Perception
- Leveraging Embedded AI to Convert Big Data into Actionable Smart Insights
- How Data Visualisation Drives Efficiency for Machine Builders
- Six Proven Strategies for Smarter Maintenance Decisions
- Top 3 Data Privacy Challenges Enterprises Must Overcome (2021‑23)
- Tableau: Turning Raw Data into Strategic Insight
- Workplace Wearables: Emerging Privacy Challenges for Employees and Employers
- Industrial Automation Drives the Shift to Intelligent Information Automation



