Bluetooth Mesh Security & Privacy: Building a Trusted IoT Network
In Parts 1 and 2 we explored Bluetooth Mesh architecture and message flow. In today’s hyper‑connected world, security isn’t optional—it’s a non‑negotiable foundation for any Mesh‑powered IoT solution.
Bluetooth SIG requires every Mesh device to implement security; disabling it is prohibited. Classic BLE point‑to‑point connections, by contrast, can operate without security if the developer chooses.
The provisioning process, which adds a device to the Mesh, and all subsequent data exchanges are engineered with security as the highest priority.
- Man‑in‑the‑Middle attacks are thwarted by Elliptic Curve Diffie‑Hellman (ECDH) key exchange during provisioning.
- Replay attacks are prevented with per‑message sequence numbers.
- Trash‑can attacks from discarded devices are neutralised via the key‑refresh (blacklisting) procedure.
The Mesh topology relies on mandatory keys that safeguard each stack layer. Let’s walk through the key security and privacy mechanisms in detail.
Provisioning: Adding an unprovisioned device to the Mesh network
A Mesh device becomes a node when it is provisioned. The device that performs provisioning—a provisioner—is typically a smartphone. The provisioner creates the network, assigns a network key, and hands out the required keys. Unprovisioned Mesh nodes advertise themselves after power‑up. The provisioner scans for these beacons and establishes a standard BLE connection (using PB‑GATT in today’s devices) to exchange keys via ECDH.
Once the session key is derived, it encrypts the network key, device key, IV index, and unicast address, which are then transmitted to the node. After successful provisioning, the node enters the configuration phase, where the provisioner discovers the node’s capabilities and assigns Application keys. A node can hold multiple Application keys; each key is bound to a specific Mesh model, ensuring that only the intended devices can decrypt the application payload.
Figure 1 illustrates the full provisioning sequence for a Dimmable Light bulb using the CYBT‑213043‑MESH Evaluation kit.
click for larger image
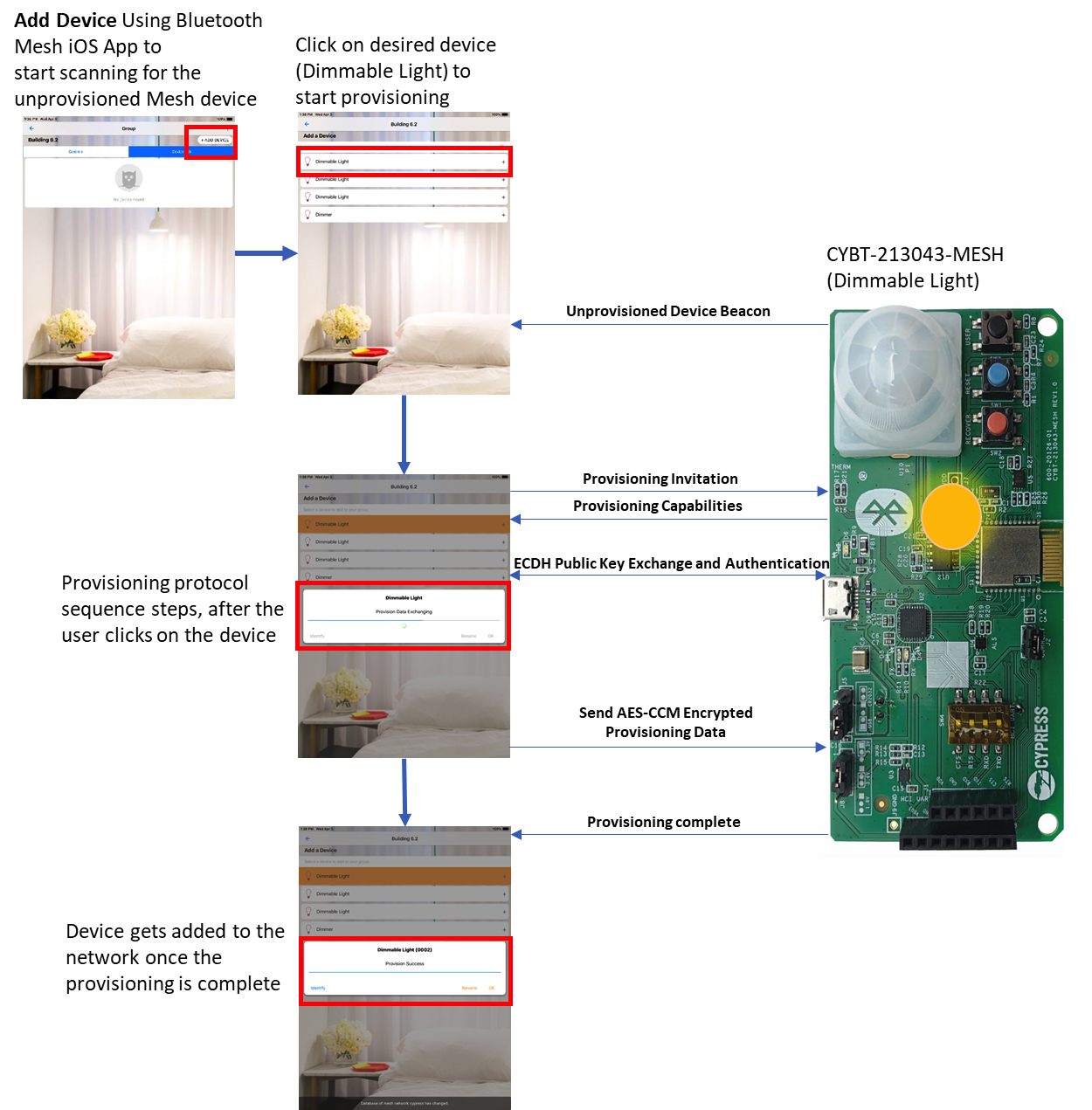
Figure 1: The Provisioning process for a Dimmable Light bulb. (Source: Cypress)
When the smartphone’s Mesh helper app selects the bulb from the unprovisioned list, it initiates the provisioning handshake. The bulb replies with its capabilities—supported elements, security algorithms, OOB options, and input/output methods. Based on these, the public keys are exchanged either via OOB or over the BLE link, followed by authentication. After the bulb is authenticated, the provisioner sends the encrypted provisioning data (network key, device key, IV index, unicast address, etc.). The node is now fully provisioned and ready for configuration.
Network, Application, and Device Keys
Network keys enable a node to decrypt and authenticate messages up to the Network layer, allowing it to relay traffic. Application keys are shared among a subset of nodes that perform similar functions; only devices holding the correct Application key can decrypt the payload. Device keys uniquely identify each provisioned node and are used solely during configuration.
Network key: A node may hold one or more Network keys, permitting the creation of multiple subnets within a single Mesh network. For example, a multi‑level parking garage can isolate each level into its own subnet, restricting relay traffic to the relevant level.
Application key: Typically shared by devices that serve the same purpose—e.g., all living‑room lights share one key, while motion sensors or locks use another. Only the devices with the appropriate key can interpret a message to change a light’s state.
Device key: Assigned during provisioning, the Device key uniquely identifies a node and is used exclusively during the configuration phase.
Node removal: Key Refresh and Blacklisting
To prevent a compromised or discarded node from re‑joining a target network—a scenario known as a Trash‑can attack—the Mesh specification defines a key‑refresh procedure. The provisioner can blacklist a node and issue new Network and Application keys to all non‑blacklisted devices. The old keys can no longer grant access, safeguarding the network against exploitation.
Privacy (Message Obfuscation)
Privacy is achieved through a privacy key derived from the Network key. The Mesh protocol uses this key to obfuscate header fields, such as the source address, thereby preventing eavesdroppers from tracking message origins.
Replay Attacks
A replay attack involves capturing a legitimate message and resending it to disrupt the network—for instance, retransmitting an unlock command to a door lock. The Mesh protocol counters this with two safeguards: the IV index and the sequence number (SEQ). Each message carries a SEQ that increments with every publish; nodes discard any packet with a SEQ equal to or less than the last valid value. The IV index must also be equal to or greater than the last processed value; otherwise, the packet is discarded. An attacker would need all relevant keys to modify these fields, making successful replays infeasible.
In summary, Bluetooth Mesh’s provisioning process guarantees that only trusted devices join the network and protects against MITM, replay, and Trash‑can attacks. Network keys enable subnetting, Application keys ensure that only the intended devices interpret payloads, and key‑refresh mechanisms safely remove compromised nodes. Privacy features conceal source addresses, while sequence numbers and IV indices prevent replay attacks. Together, these mechanisms establish Bluetooth Mesh as a highly secure and private platform for IoT deployments.
In Part 3, we’ll discuss how to choose the right Bluetooth Mesh device for your specific application.
Embedded
- Enhance SaaS and Cloud Security with Automated Testing and Performance Monitoring
- Bluetooth Mesh Design: Understanding Nodes, Features, and Interoperability
- Bluetooth Mesh Node Communication: Designing Robust Mesh Networks
- Choosing the Right Device for Bluetooth Mesh: A Practical Guide to Hardware, Software, and App Requirements
- Bluetooth Mesh Design Choices: Module vs. Discrete Device
- Cypress Launches Dual‑Mode Bluetooth 5.0 MCUs with Mesh Networking, Bridging IoT Devices to Smartphones
- Future Electronics Forms Global Partnership with Silvair to Accelerate Bluetooth Mesh Solutions
- Contrinex 2020: Cloud-Ready Sensors & Bluetooth Light Curtains for Safety
- Can Security and Privacy Hinder the IoT Revolution?
- Arduino‑Powered Smart Coffee Maker with Bluetooth Control and Temperature Monitoring



